- AI

AI Task Automation: How to Save Time Every Day in 2026
Learn how AI task automation can reclaim up to 2 hours of your day in 2026. This guide provides a…
Read More - AI Threats

Ransomware 3.0 in 2026: How Double Extortion and RaaS Are Targeting Your Business
Ransomware was present in 44% of all breaches in 2026 — a 37% surge from the prior year. RaaS has…
Read More - AI

AI Agent Workflows: How Autonomous Systems Execute Complex Tasks Without Apps (2026)
"Master the mechanics of AI agent workflows in 2026. This guide explains how autonomous systems use task decomposition, API orchestration,…
Read More - AI

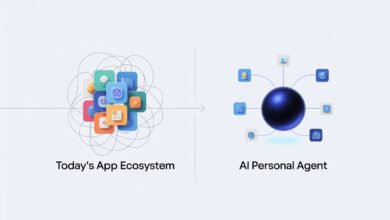
AI Personal Agents for Productivity Automation
Discover 7 powerful ways AI personal agents for productivity are transforming work in 2026. Learn how autonomous assistants navigate complex…
Read More - AI Threats

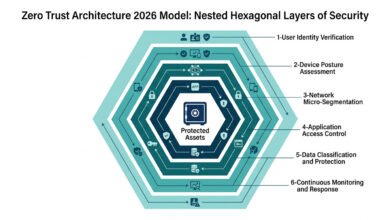
Zero Trust Architecture 2026: The Essential Implementation Guide for IT Teams
81% of organisations are actively implementing zero trust architecture in 2026 — and those that have report 50% lower breach…
Read More - AI

Will AI Personal Agents Replace Apps? The Complete Guide for 2026
In 2026, AI personal agents are transforming the digital landscape, moving beyond simple voice assistants to proactive, autonomous interfaces. This…
Read More - AI Threats

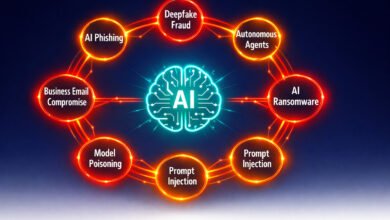
AI-Powered Cyberattacks 2026: 7 Proven Threats Every Business Must Know
AI-powered cyberattacks surged 72% in the past year—and 87% of organizations have already been hit. From autonomous AI agents to…
Read More - PQC

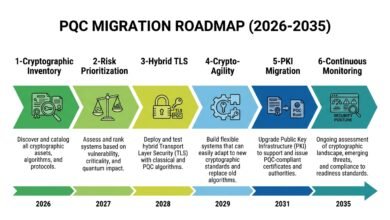
Post-Quantum Cryptography Migration Roadmap (PQC): The Complete 6-Phase Enterprise Implementation Guide for 2026
Most enterprises know they need to migrate to post-quantum cryptography — but few have a structured plan to do it.…
Read More - AI Threats

Cybersecurity in 2026: The Most Dangerous AI Threats, Zero Trust Failures, and Hidden Risks
AI-powered attacks, deepfake fraud, and ransomware evolution have made cybersecurity in 2026 the most complex threat environment in history. Organisations…
Read More - PQC

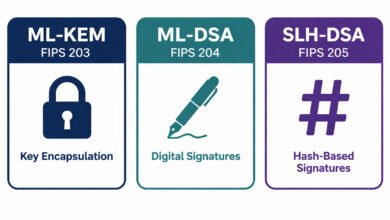
ML-KEM vs ML-DSA vs SLH-DSA: The Complete Algorithm Selection Guide for 2026
NIST finalized three post-quantum cryptography standards in August 2024 — but ML-KEM, ML-DSA, and SLH-DSA serve entirely different functions. This…
Read More - PQC

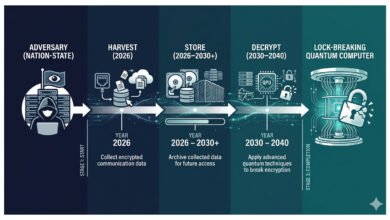
Harvest Now, Decrypt Later (HNDL) Attacks Explained: Why Your Encrypted Data Is Already at Risk in 2026
Nation-states are collecting your encrypted data right now — not to read it today, but to decrypt it once quantum…
Read More - PQC

Post-Quantum Cryptography (PQC) 2026: Why Your Encryption Strategy Must Change Now
Nation-states are harvesting your encrypted data today — storing it to decrypt the moment a quantum computer arrives. Post-quantum cryptography…
Read More