Cybersecurity in 2026: The Most Dangerous AI Threats, Zero Trust Failures, and Hidden Risks

It is 8 a.m. Your organisation’s email system is down. An AI-generated phishing campaign has compromised three executive accounts simultaneously. A poisoned software update is propagating through your development pipeline. Ransomware has locked your backup servers. This is not a hypothetical scenario — it is the operating reality of cybersecurity in 2026.
The threats are faster, more autonomous, and more precisely targeted than any prior generation of attack. The organisations that survive this environment are not the ones with the largest security budgets. They are the ones who understand the threat landscape clearly and act with architectural discipline. This complete guide to cybersecurity in 2026 synthesises the latest findings from PwC, IBM X-Force, Gartner, and the FBI to give your organisation the intelligence it needs to build genuine digital resilience.
⚠ DISCLAIMER This article is for educational and informational purposes only. It does not constitute professional cybersecurity advice, a security audit, or a specific product recommendation. Organisations should engage qualified cybersecurity professionals before implementing architectural or policy changes. Threat statistics cited reflect published research and may not reflect your specific sector, geography, or risk profile.
What Is Cybersecurity in 2026? Understanding the New Threat Landscape
The practice of cybersecurity in 2026 has undergone a structural transformation. The traditional model — perimeter defence, firewall-and-antivirus, reactive patching — has been rendered functionally obsolete by three concurrent forces: the weaponisation of artificial intelligence by threat actors, the dissolution of the network perimeter through cloud migration and remote work, and the emergence of autonomous attack agents capable of executing full attack sequences without human direction.
The PwC Annual Threat Dynamics 2026 frames this shift precisely: AI is no longer an enhancement to attack toolkits — it is the core tradecraft. [1] Threat actors use AI to automate reconnaissance, craft hyper-personalised phishing campaigns, accelerate malware development, and scale social engineering across languages and geographies simultaneously. The window between the public release of an AI capability and its weaponisation has shrunk from months to days.
The Scale of the Problem in Numbers
The quantitative picture is unambiguous. The global average cost of a data breach reached $4.88 million in the most recent IBM reporting period[2]. Cybercrime losses reported to the FBI exceeded $16.6 billion — a 33% increase from the prior year [3]. 68% of organisations experienced data leaks linked to AI tool usage, yet only 23% had formal security policies governing those tools at the time of the incident. Against this backdrop, digital resilience — the capacity to anticipate, withstand, and recover from cyberattacks — has become a board-level strategic priority, not a technical afterthought.
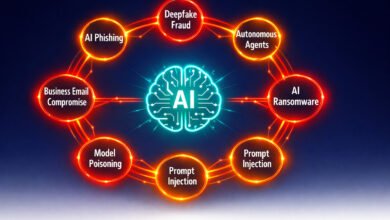
AI-Powered Cyberattacks — The Dominant Threat Vector in Cybersecurity 2026
No single development has reshaped the cybersecurity 2026 threat landscape more profoundly than the mass adoption of AI by adversaries. AI-powered cyberattacks are not a future risk category — they are the present operating environment. Gartner identifies AI-specific threats as the number one emerging risk category for enterprise security functions this year.
AI-Generated Phishing at Scale
Large language models now enable threat actors to deploy phishing campaigns of extraordinary personalisation and volume. Where traditional phishing relied on mass, generic lures, AI-generated phishing synthesises information scraped from LinkedIn profiles, corporate websites, and social media to produce contextually accurate messages that impersonate colleagues, clients, or executives. These emails bypass traditional spam filters because they contain no generic indicators of compromise. 85% of organisations experienced at least one deepfake fraud incident in the past year, according to industry survey data [4].
Autonomous AI Agents as Attack Vectors
Perhaps the most consequential emerging threat in cybersecurity 2026 is the autonomous AI agent deployed as an offensive tool. OpenAI and Google DeepMind both identified agentic AI systems as their primary near-term safety concern, with researchers demonstrating that compromised AI agents can exfiltrate data, escalate privileges, and traverse networks laterally — all without human intervention. Most current enterprise security stacks are entirely unprepared to detect this attack pattern [5]. Palo Alto Networks frames this directly: adversaries will no longer make humans their primary target. They will target the agents.
Deepfakes and the Identity Crisis
Generative AI has achieved a state of near-flawless real-time replication. Deepfake video and voice cloning now enable threat actors to impersonate CEOs, financial controllers, or IT administrators in real time, commanding wire transfers, credential resets, or system access with apparent authenticity. This has created what security practitioners are calling a crisis of identity: verifying that a voice on the phone, a face on a video call, or a message in an inbox is genuinely human and genuinely who it claims to be has never been more technically challenging.
Table 1: AI-Powered Attack Types — Mechanisms, Targets, and Defensive Responses
| Attack Type | AI Mechanism | Primary Target | Defensive Response |
| AI Phishing / Spear Phishing | LLM personalisation at scale | Employees, executives | AI-based email filtering, security awareness training |
| Deepfake Fraud | Generative video/voice synthesis | Finance, HR, C-suite | Multi-factor voice verification, callback protocols |
| Autonomous Agent Attacks | Prompt injection, tool misuse | AI systems, API endpoints | Zero Trust for non-human identities, agent monitoring |
| AI-Enhanced Ransomware | Automated target selection, encryption | SMBs, healthcare, critical infra | Immutable backups, EDR, network segmentation |
| Model Poisoning | Training data manipulation | AI/ML pipelines | AI-SPM tools, adversarial testing (red teaming) |
| Automated Vulnerability Discovery | Code analysis at speed | Web apps, cloud infra | Continuous scanning, patch velocity programmes |
💡 For more information, explore the complete segments of our AI Threats Security Series.
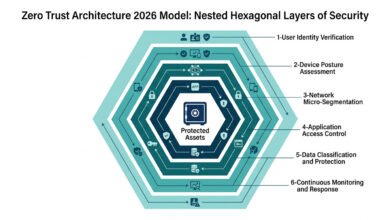
Zero Trust Architecture — Why the Perimeter Is Dead and What Replaces It
The principle underpinning zero trust architecture is deceptively simple: never trust, always verify. Every access request — regardless of whether it originates inside or outside the network — is treated as potentially hostile until verified through continuous authentication, device posture assessment, and least-privilege enforcement. This model did not emerge from academic theory. It emerged from the empirical failure of perimeter-based security in a world where 82% of organisations now operate in hybrid or multi-cloud environments, and remote work has become structurally permanent.
The Business Case Is Now Quantified
The ROI for zero trust implementation is no longer theoretical. Organisations that have fully deployed zero trust architecture report 50% fewer successful lateral movement attacks compared with perimeter-defended environments [6]. In 2026, organisations implementing combined Zero Trust AI Security reported 76% fewer successful breaches and reduced incident response times from days to minutes. [6] Gartner projects that organisations adopting Continuous Exposure Management — a zero trust adjacent practice — will be 3× less likely to experience a breach.
Identity as the New Control Plane
Within the zero trust model, identity and access management have become the primary control plane. IBM X-Force identifies credential abuse as among the most persistent and prevalent attack vectors year after year. The PwC Threat Dynamics 2026 report projects that identity will remain the primary attack vector even as zero trust adoption grows — because adversaries are evolving: spoofing device posture, abusing non-human identities, and targeting AI-driven automated workflows. Zero trust without mature IAM security is architecturally incomplete.
Non-Human Identities — The Blind Spot
Machine identities — service accounts, API tokens, OAuth grants, workload identities — now outnumber human employee identities by a significant multiple in most enterprise environments. These non-human identities are frequently over-privileged, rarely audited, and seldom subject to the same authentication rigour as human accounts. They represent the largest unaddressed identity attack surface in cybersecurity in 2026. Extending zero trust principles to non-human identities is the most consequential unfulfilled mandate facing enterprise security teams this year.
Ransomware 3.0 — RaaS, Double Extortion, and AI-Enhanced Attacks in 2026
Ransomware has undergone three evolutionary generations. The first generation encrypted files and demanded payment. The second generation added data exfiltration — pay or your data is published. The third generation, Ransomware 3.0, combines AI-enhanced target selection, Ransomware-as-a-Service (RaaS) distribution models, triple and quadruple extortion schemes, and automated lateral movement to create an attack class of dramatically increased lethality and scalability.
Ransomware as a Service — The Industrialisation of Cybercrime
RaaS has transformed ransomware 2026 from a specialist criminal discipline into an accessible commodity. Ransomware developers lease their attack infrastructure to affiliate networks — providing technical tooling, negotiation support, and payment processing in exchange for a revenue share. This model has dramatically lowered the technical barrier to entry for threat actors, expanding the total pool of potential attackers while increasing attack volume and variety.
Healthcare, critical infrastructure, education, and small-to-medium enterprises remain disproportionately targeted due to the combination of high-value data and historically under-resourced security postures.
AI-Accelerated Ransomware Deployment
AI integration in ransomware 2026 operates across multiple phases of the attack chain. In the reconnaissance phase, AI tools analyse target organisations’ public digital footprint to identify the highest-value data assets and the most vulnerable credential surfaces.
In the lateral movement phase, machine learning models identify privilege escalation pathways faster than human analysts can detect them. In the encryption phase, AI selects which file types and which systems to prioritise based on operational disruption impact — maximising negotiating leverage against the victim.
Identity and Access Management — The New Firewall in Cybersecurity 2026
The phrase “identity is the new firewall” has become the defining axiom of cybersecurity 2026. It reflects a fundamental shift in the attack surface. In the perimeter era, breaches required defeating a boundary. In the identity era, breaches require defeating a credential, and credentials are far more accessible. They are phished, purchased on dark web marketplaces, leaked in third-party breaches, or simply guessed through credential stuffing automation.
The Four Pillars of Modern IAM Security
Multi-Factor Authentication (MFA) Beyond SMS: SMS-based MFA is now considered a weak second factor due to SIM-swapping attacks. The 2026 standard is phishing-resistant MFA — hardware security keys, passkeys, and device-bound authentication tokens that cannot be intercepted or replicated through social engineering.
Privileged Access Management (PAM): Privileged accounts — those with administrative or root-level access — must be governed through dedicated PAM solutions that enforce just-in-time access, session recording, and credential vaulting. These accounts represent the highest-value targets in any environment.
Adaptive Authentication: Risk-based authentication systems continuously evaluate contextual signals — device posture, geolocation, behaviour patterns, time of access — and elevate authentication requirements when anomalies are detected. This creates a dynamic trust threshold that responds to real-time threat signals.
Non-Human Identity Governance: Service accounts, API keys, OAuth grants, and agent credentials must be subject to the same governance rigour as human identities. Automated discovery, rotation, and least-privilege enforcement for Non-human identity security in enterprise environments has become the most consequential unaddressed gap in cybersecurity in 2026. Machine identities — service accounts, API tokens, OAuth grants, workload identities — now outnumber human employee identities by a significant multiple in most enterprise environments.
Table 2: Identity and Access Management Controls — Current State vs. 2026 Best Practice
| IAM Control | Legacy Practice (Pre-2024) | 2026 Best Practice | Risk Addressed |
| Authentication | Password + SMS OTP | Phishing-resistant MFA / Passkeys | SIM swap, phishing, credential theft |
| Privileged Access | Standing admin accounts | Just-in-time PAM with session recording | Credential abuse, lateral movement |
| Non-Human Identities | Long-lived static API keys | Short-lived tokens, automated rotation | Token theft, service account abuse |
| Session Management | Fixed-duration tokens | Continuous adaptive re-authentication | Session hijacking, stolen tokens |
| Access Reviews | Annual manual review | Continuous automated entitlement review | Privilege creep, orphaned accounts |
| Identity Threat Detection | SIEM-based log monitoring | AI-driven ITDR with behavioural baseline | Insider threats, credential anomalies |
💡 For more information, explore the complete segments of our AI Threats Security Series.
Post-Quantum Cryptography Migration Planning 2026 — Why Your Encryption Strategy Must Change Now
Quantum computing does not yet represent an operational threat to current encryption standards. But the post-quantum cryptography challenge cannot wait until the quantum threat becomes operational. The reason is a strategy known as “Harvest Now, Decrypt Later” (HNDL): nation-state adversaries are actively exfiltrating encrypted data today, storing it, and positioning to decrypt it the moment sufficiently capable quantum computers become available. Data with a long security lifespan — government communications, healthcare records, financial contracts, intellectual property — is already at risk from HNDL operations.
The NIST Post-Quantum Standards — What Organisations Must Know
NIST finalised its first set of quantum-safe encryption standards in 2024, providing organisations with concrete cryptographic primitives designed to resist quantum attacks. The three primary standards — ML-KEM / FIPS 203 (key encapsulation), ML-DSA / FIPS 204 (digital signatures), and SLH-DSA / FIPS 205 (hash-based signatures) — are available for implementation now. Gartner recommends that organisations targeting quantum readiness by 2030 must begin cryptographic inventory and migration planning no later than this year.
Table 3: Major Cybersecurity Frameworks and Their 2026 Applicability
| Framework | Issuing Body | Primary Focus | 2026 Relevance |
| NIST CSF 2.0 | NIST (US) | Identify, Protect, Detect, Respond, Recover + Govern | Universal baseline — all organisation sizes |
| Zero Trust Architecture (SP 800-207) | NIST (US) | Never trust, always verify — network and identity | Critical for hybrid/cloud environments |
| AI Risk Management Framework | NIST (US) | Adversarial AI testing, model governance | Mandatory for AI deployments |
| NIS2 Directive | European Union | Operational resilience, incident reporting | Compliance requirement for EU operations |
| DORA | European Union | Digital operational resilience for the financial sector | Mandatory for EU financial services |
| MITRE ATT&CK | MITRE Corporation | Adversary tactics, techniques, procedures (TTPs) | Threat modelling, red team exercises |
| ISO 27001:2022 | ISO/IEC | Information security management systems | Certification and governance standard |

Counter-Arguments: Three Challenges to the 2026 Cybersecurity Consensus
A credible analysis of cybersecurity in 2026 must engage honestly with the legitimate counterpoints to prevailing consensus positions.
1. Threat Inflation or Genuine Escalation?
Ongoing debate questions whether the apparent rise in cyber threats reflects a true escalation or an industry-driven amplification of risk. The cybersecurity sector does have structural incentives to emphasize threats, and some vendor-reported metrics conflate minor incidents with significant breaches. However, independently verified data — particularly from law enforcement agencies and rigorously audited industry reports — points to a real increase in both the frequency and financial impact of cybercrime. The escalation is therefore substantive, though its exact magnitude varies by sector and requires independent validation.
2. Zero Trust for SMBs: Practical Strategy or Overstated Ideal?
Zero trust is frequently perceived as a complex, resource-intensive framework, seemingly beyond the reach of small and medium-sized businesses. This view, however, overlooks the adaptability of its core principles — strong identity verification, least-privilege access, network segmentation, and continuous monitoring.
These elements can be implemented incrementally and aligned with available resources. Modern cloud-based identity platforms have significantly reduced implementation complexity, making zero trust less of a fixed architecture and more of a scalable model that evolves with organizational capacity.
3. Post-Quantum Cryptography: Strategic Priority or Premature Diversion?
Immediate threats such as phishing, ransomware, and unpatched vulnerabilities continue to pose far greater operational risks for most organizations than quantum-enabled attacks. Nevertheless, the “harvest now, decrypt later” scenario introduces a long-term strategic concern, particularly for data requiring extended confidentiality.
As a result, the urgency of post-quantum cryptography depends on context. Organizations in sectors such as government, defense, healthcare, and finance must prioritize early planning, while others can begin with cryptographic inventories without diverting resources from more immediate threats.
Practical Cybersecurity Roadmap for 2026 — Where to Start
The breadth of the cybersecurity 2026 challenge can make prioritisation feel paralysing. The following phased approach, informed by NIST CSF 2.0 and CIS Controls v8, provides a sequenced starting point applicable to organisations of most sizes and sectors.
Phase 1 — Immediate Actions (0–90 Days)
Deploy phishing-resistant MFA: Replace SMS-based second factors with hardware keys or passkeys across all privileged and internet-facing accounts. This single control eliminates the most prevalent vector for credential theft.
Conduct an identity audit: Inventory all human and non-human accounts. Identify dormant accounts, over-privileged service accounts, and long-lived API keys. Revoke or restrict anything that cannot be justified by operational necessity.
Test your backup recovery: Ransomware preparedness is only as strong as your last verified recovery test. Immutable, offline backups tested for recoverability within defined RTOs are non-negotiable.
Phase 2 — Strategic Investments (90 Days–12 Months)
Begin zero-trust architecture planning: Map your most critical data flows and implement micro-segmentation around them. Extend identity verification requirements to all access requests regardless of network origin.
Deploy AI-aware monitoring: Implement behavioural analytics tools capable of detecting anomalous AI agent activity, unusual API call patterns, and lateral movement that traditional signature-based tools miss.
Begin cryptographic inventory: Identify all encryption implementations across your environment. Flag those using RSA-2048 or EC-based schemes and begin planning migration sequencing toward NIST post-quantum standards.
Phase 3 — Continuous Resilience (Ongoing)
Cybersecurity in 2026 is not a destination — it is a continuous operational discipline. Red team exercises, tabletop simulations, threat intelligence subscriptions, and regular third-party assessments are not optional luxuries. They are the mechanisms through which organisations maintain calibration against an evolving threat environment. Digital resilience is built through repeated, deliberate practice — not achieved through a single implementation project.
KNOWLEDGE ASSESSMENT QUIZ: How Prepared Is Your Organisation for Cybersecurity in 2026? Knowledge Assessment — Organisational Cybersecurity Readiness
Disclaimer: This quiz is for self-awareness only and does not constitute a clinical assessment, security audit, or professional recommendation.
Q1: Has your organisation deployed phishing-resistant MFA (hardware keys or passkeys) for all privileged accounts?
A) Yes — fully deployed across all privileged and internet-facing accounts
B) Partially — deployed for some accounts but not all
C) No — we use SMS-based 2FA or passwords only
D) We have not assessed our current MFA posture
Q2: Does your organisation have a documented and tested incident response plan for a ransomware attack?
A) Yes — tested within the last 12 months with verified recovery times
B) Yes — documented but not recently tested
C) Partially — we have some procedures, but no formal plan
D) No formal plan exists
Q3: Has your organisation conducted a formal inventory of non-human identities (service accounts, API keys, OAuth grants)?
A) Yes — fully inventoried and under continuous governance
B) Partially — we know the major ones, but not all
C) No — we have not formally inventoried non-human identities
D) We are not sure what non-human identities we have
Q4: How would you characterise your organisation’s current approach to zero trust architecture?
A) Fully implemented — continuous verification for all access requests
B) In progress — we have begun deployment in key areas
C) Planned — we have a roadmap, but have not yet begun implementation
D) We operate a perimeter-based security model
Q5: Has your security team received specific training on detecting AI-generated phishing and deepfake fraud?
A) Yes — within the last 6 months, including practical simulations
B) Partially — general phishing training only
C) No — our training programme has not been updated for AI threats
D) We do not have a regular security awareness training programme.
Score Interpretation:
Mostly A: Your organisation demonstrates strong foundational readiness. Focus on continuous improvement, red team exercises, and post-quantum planning.
Mostly B: You have partial controls in place. Prioritise closing the identified gaps in MFA, incident response testing, and identity governance.
Mostly C/D: Significant exposure exists across multiple vectors. Engage a qualified cybersecurity professional to conduct a structured gap assessment and prioritise immediate remediation actions.
Final Thoughts
Cybersecurity in 2026 is not a problem that technology alone will solve. The organisations that navigate this environment successfully share three characteristics: they understand the threat landscape with factual precision rather than generalised anxiety; they build security architecture on sound principles — zero trust, identity governance, layered defence — rather than on point solutions; and they treat security as a continuous operational discipline rather than a periodic project.
The convergence of AI-powered attacks, autonomous agents, identity exploitation, and quantum risk creates an unprecedented threat surface. But it also creates a clarity of priorities. AI-powered cyberattacks require AI-capable defences.
Architecture requires identity-first thinking. Ransomware 2026 requires resilience by design. Post-quantum cryptography requires planning that begins now. None of these is optional. All of them are achievable. The question is sequencing and commitment, not capacity.
Engage qualified cybersecurity professionals, begin with the foundational controls in Phase 1 of the roadmap above, and build systematically toward the digital resilience that the 2026 threat environment demands.
FAQ
Q1: What is the single most important cybersecurity action an organisation should take in 2026?
A: Deploying phishing-resistant multi-factor authentication across all privileged and internet-facing accounts. Credential theft — through AI-generated phishing, social engineering, and dark web purchases — remains the most common initial access vector in cybersecurity 2026. Eliminating reusable passwords and SMS-based OTP as authentication factors closes the largest single attack surface immediately and at relatively low cost.
Q2: How does zero-trust architecture differ from traditional network security?
A: Traditional security assumes that traffic inside the network perimeter can be trusted. Zero trust architecture assumes that no traffic — internal or external — is trusted by default. Every access request is verified through identity, device posture, and least-privilege enforcement before being granted. This model directly addresses the modern threat reality where perimeters have dissolved through cloud migration, remote work, and supply chain connectivity.
Q3: Are small businesses genuinely at risk from AI-powered cyberattacks?
A: Yes — and disproportionately so. AI-powered attack tools enable threat actors to scale personalised attacks across thousands of targets simultaneously, making the economics of targeting SMBs viable in ways they were not previously.
Ransomware-as-a-Service models explicitly target SMBs because they typically combine high-value data with lower security maturity. The RaaS cybersecurity ecosystem has professionalised SMB targeting into a systematic industrial process.
Q4: When will post-quantum computing actually threaten current encryption?
A: Most cryptographic experts place the arrival of cryptographically relevant quantum computers — capable of breaking RSA-2048 or ECC-256 — somewhere between 2030 and 2035.
However, the Harvest Now Decrypt Later attack strategy means data with long confidentiality requirements is already at risk today. Organisations handling sensitive data over multi-year timescales should begin planning for a post-quantum cryptography migration now, regardless of when the quantum threat becomes operational.
Q5: What is the difference between EDR, XDR, and MDR in cybersecurity 2026?
A: Endpoint Detection and Response (EDR) monitors and responds to threats on individual endpoints — laptops, servers, workstations. Extended Detection and Response (XDR) integrates telemetry across endpoints, network, cloud, and identity into a unified detection and response platform.
Managed Detection and Response (MDR) provides EDR or XDR capabilities as a managed service with 24/7 human analyst oversight. For most organisations without dedicated security operations centres, MDR represents the most practical path to enterprise-grade threat detection in cybersecurity 2026.
Q6: How should organisations approach cybersecurity compliance in 2026, given the proliferation of new regulations?
A: The regulatory landscape in 2026 includes NIS2 (EU), DORA (EU financial services), CIRCIA (US critical infrastructure), and the expanding AI governance frameworks from NIST and the EU AI Act.
Rather than managing each regulation independently, organisations benefit from aligning to a comprehensive baseline framework — NIST CSF 2.0 or ISO 27001:2022 — that maps to multiple regulatory requirements simultaneously. A structured digital resilience programme built on such a baseline satisfies most regulatory requirements as a by-product of sound security practice.
AI Threats Series Overview
This article is part of the AI Threats Security Series — a technical collection of guides exploring the most dangerous AI-powered attack categories, defensive frameworks, and the steps organizations must take to build resilient security postures in 2026.
References
- [1] PwC Annual Threat Dynamics 2026. Identity attacks surge as AI reshapes cyber threat landscape. Industrial Cyber.
- https://industrialcyber.co/reports/pwc-annual-threat-dynamics-2026-discloses-that-identity-attacks-surge-as-ai-reshapes-cyber-threat-landscape/
- [2] IBM Security. Cost of a Data Breach Report 2024. IBM.
https://www.ibm.com/reports/data-breach - [3] FBI Internet Crime Complaint Center (IC3). 2024 Internet Crime Report. FBI IC3. https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf
- [4] Entrust. 2025 Identity Fraud Report — Deepfake Incidents: https://www.entrust.com/resources/report/2025-identity-fraud-report
- [5] NIST. AI Risk Management Framework (AI RMF 1.0): https://www.nist.gov/system/files/documents/2023/01/26/AI%20RMF%201.0.pdf
- [6] Forrester Research. The Total Economic Impact of Zero Trust. 2026. https://www.forrester.com/report/the-total-economic-impact-of-zero-trust/