Post-Quantum Cryptography Migration Roadmap (PQC): The Complete 6-Phase Enterprise Implementation Guide for 2026
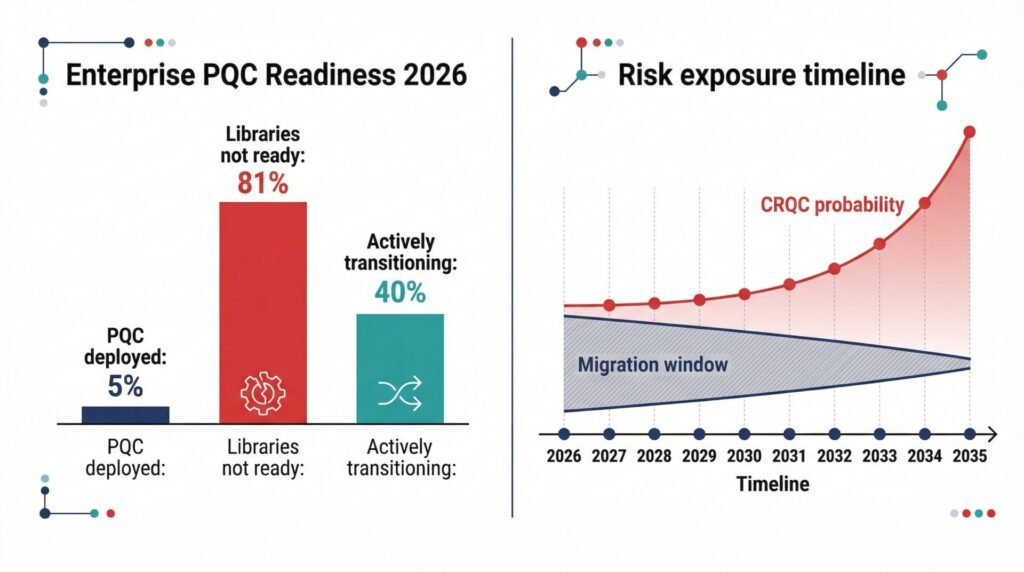
In 2026, only 5 percent of enterprises have deployed quantum-safe encryption [2], despite the National Institute of Standards and Technology finalizing post-quantum cryptography (PQC) standards in August 2024 [1]. At the same time, 81 percent of organizations report that their cryptographic libraries and hardware security modules are not yet ready for PQC integration [2]. This widening gap between awareness and execution is now the defining challenge for security leaders.
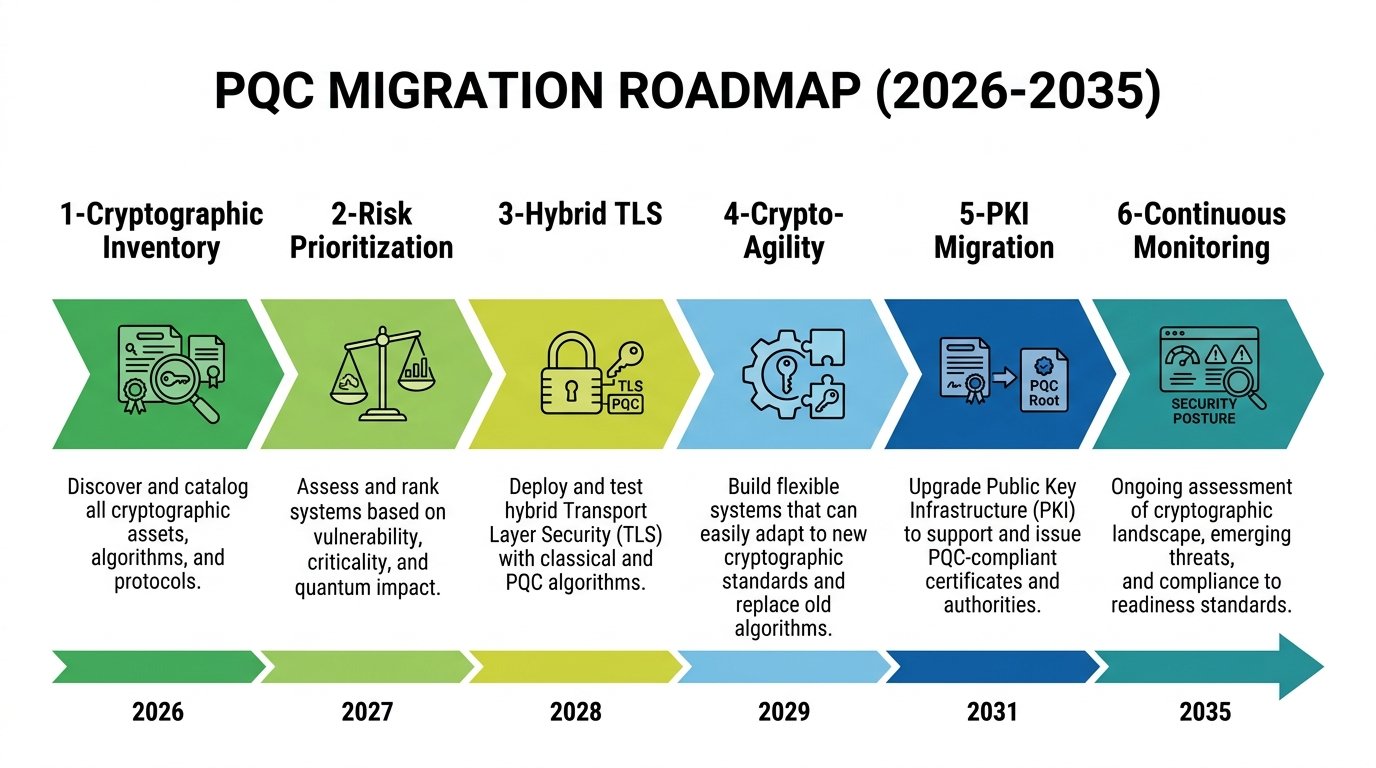
Executing a post-quantum cryptography migration roadmap is not a one-time project — it is a multi-year program that requires organisations to sequence six distinct phases in the correct order: cryptographic inventory, risk prioritisation, hybrid TLS deployment, crypto-agility engineering, PKI migration, and continuous monitoring. Each phase in this post-quantum cryptography migration roadmap builds directly on the previous one, and skipping any phase creates architectural gaps that will extend quantum exposure well beyond the 2035 deprecation deadline.
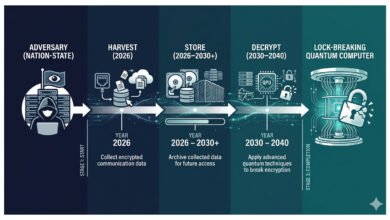
A structured post-quantum cryptography migration roadmap is therefore essential. Without a clearly defined, phased approach, organizations risk falling behind regulatory timelines and extending their exposure to “harvest now, decrypt later” (HNDL) threats well into the quantum era. The transition is not a single upgrade, but a multi-year transformation requiring coordination across infrastructure, applications, and governance.
This post-quantum cryptography migration roadmap provides a structured, phase-based framework that translates the urgency of the quantum threat into a practical, sequenced program — one that can be executed, measured, audited, and aligned with enterprise governance at every phase.
⚠ Technical Disclaimer: This article is for educational and informational purposes only. It does not constitute professional cybersecurity, cryptographic, or legal advice. Organizations should engage qualified professionals before implementing cryptographic changes.
Grounded in NIST SP 1800-38C guidance [3], the CNSA 2.0 compliance timeline [4], and regulatory requirements across the U.S., EU, Australia, and Canada [5], this guide presents a complete 6-phase enterprise implementation framework. Each phase defines specific actions, deliverables, and timelines, enabling organizations to move from fragmented awareness to a coordinated, compliant migration strategy. For a deeper analysis of the quantum threat model — including HNDL and Mosca’s Theorem — refer to the pillar guide: Post-Quantum Cryptography 2026: Why Your Encryption Strategy Must Change Now.
The 6-Phase Post-Quantum Cryptography Migration Roadmap — Overview
The migration from classical to quantum-safe cryptography is not a single project. It is a multi-year program that spans discovery, risk assessment, protocol migration, architectural modernization, PKI replacement, and continuous governance. NIST SP 1800-38 — produced with 47 industry collaborators, including AWS, IBM, Microsoft, JPMorgan Chase, and Thales — frames the migration challenge around two core workstreams: cryptographic discovery (finding all quantum-vulnerable usage) and interoperability testing (validating that post-quantum replacements work in production protocols)[3]. The 6-phase roadmap below synthesizes this guidance with current enterprise deployment experience and the binding regulatory timelines now in force across multiple jurisdictions.
Table 1: The complete 6-phase post-quantum cryptography migration roadmap — phase name, timeline, core actions, and key deliverables.
| Phase | Timeline | Name | Core Actions | Key Deliverable |
| 1 | 0–3 months (Now) | Cryptographic Inventory | Map all RSA, ECC, and DH usage across applications, protocols, HSMs, certificates, APIs, cloud endpoints, and vendor dependencies. Create Crypto Bill of Materials (CBOM). | Complete CBOM with risk classification by data sensitivity and confidentiality lifetime |
| 2 | 1–3 months | Risk Prioritization | Score all cryptographic assets by HNDL exposure (data lifetime × migration complexity). Classify as Immediate / Medium / Low priority. Align with CNSA 2.0 or NIST IR 8547 timelines. | Risk-ranked migration backlog with compliance deadline mapping |
| 3 | 3–12 months | Hybrid TLS Deployment | Deploy ML-KEM-768 + X25519 hybrid key exchange on all internet-facing TLS services. Validate performance and interoperability. Extend to VPN and SSH configurations. | Internet-facing HNDL exposure eliminated for new traffic |
| 4 | 6–24 months | Crypto-Agility Engineering | Redesign new systems with algorithm-agnostic interfaces. Eliminate hardcoded RSA/ECC. Apply NIST SP 800-131A Rev. 3 architectural standards. Establish cryptographic governance policy. | All new systems are deployable with algorithm substitution via configuration |
| 5 | 12–36 months | PKI and Certificate Migration | Replace RSA/ECDSA certificates with ML-DSA across TLS leaf, intermediate, and root CAs. Coordinate with certificate authorities. Pilot hybrid X.509 certificates. Update HSMs. | Full PKI chain migrated to ML-DSA; hybrid certificates in production |
| 6 | Ongoing | Continuous Monitoring | Automated scanning for quantum-vulnerable algorithm usage. Certificate lifecycle tracking. Algorithm compliance reporting. Preparedness for SLH-DSA fallback if lattice weaknesses emerge. | Continuous cryptographic posture maintenance through the 2035 deprecation deadline |
💡 For more information, explore the complete segments of our PQC Series
Phase 1 and 2 — Cryptographic Inventory and Risk Prioritization
No migration decision can be made without knowing what needs to be migrated. Within any post-quantum cryptography migration roadmap, the Crypto Bill of Materials (CBOM) — a comprehensive inventory of every cryptographic asset across an enterprise — is the deliverable that makes all subsequent phases actionable. NIST SP 1800-38B defines the cryptographic discovery workstream as the foundational activity for PQC migration[3], noting that organizations frequently discover hundreds or thousands of instances of quantum-vulnerable cryptography when automated scanning tools are deployed — far more than manual assessment processes reveal.
The CBOM must extend beyond application-layer certificates to cover every protocol, key, and vendor dependency where RSA, ECC, or Diffie-Hellman is used. A structured post-quantum cryptography migration roadmap requires this level of visibility to enable prioritization and phased execution. NIST CSWP 39 defines crypto-agility as a core architectural goal of the migration[6], and agility is impossible without first knowing where classical algorithms are embedded. Table 3 maps the seven asset categories that a complete CBOM must cover.
Table 2: Regulatory compliance matrix — six major PQC frameworks, their scope, key deadlines, and alignment with the 6-phase migration roadmap.
| Framework / Mandate | Who It Applies To | Key PQC Deadline | Roadmap Phase Alignment |
| NSA CNSA 2.0 | U.S. National Security Systems; defense contractors; intelligence community | New systems: Jan 2027 (ML-KEM + ML-DSA) Full application migration: 2030 Complete infrastructure: 2035 | Phases 1–2 required immediately; Phase 3 (hybrid TLS) by 2025–2026; Phase 5 (PKI) by 2030 |
| NIST IR 8547 (deprecation timeline) | All U.S. federal agencies; FISMA-regulated organizations; cascades to contractors | Deprecate quantum-vulnerable algorithms: 2030 Disallow all RSA/ECC in federal use: 2035 | Phases 1–3 must be completed by 2028; Phases 4–5 by 2030–2033 |
| White House NSM-10 (May 2022) | All U.S. national security systems, agency-wide federal systems | Full quantum-safe migration of all federal systems: 2035 Inventory and planning: required annually from 2023 | Phases 1–2 compliance required now; aligns with full 6-phase completion by 2035 |
| EU Coordinated PQC Roadmap (2025) | EU Member States; regulated industries in NIS2 and DORA scope | Initial roadmaps: Dec 2026, High-risk systems: Dec 2030, Full transition: Dec 2035 | Phase 1–2 by the end of 2026; Phases 3–4 by 2028–2030; Phases 5–6 by 2035 |
| Australia ASD Information Security Manual | Australian government systems; critical infrastructure operators | Classical asymmetric crypto eliminated: end of 2030 Migration plan: end of 2026 | Most aggressive commercial timeline — Phases 1–5 must be complete by the end of 2030 |
| Canada Cyber Centre PQC Roadmap (2025) | Canadian federal departments and agencies | Initial migration plan: April 2026, High-priority systems: end of 2031, All systems: end of 2035 | Phase 1–2 completion required April 2026; aligns with 6-phase structure through 2035 |
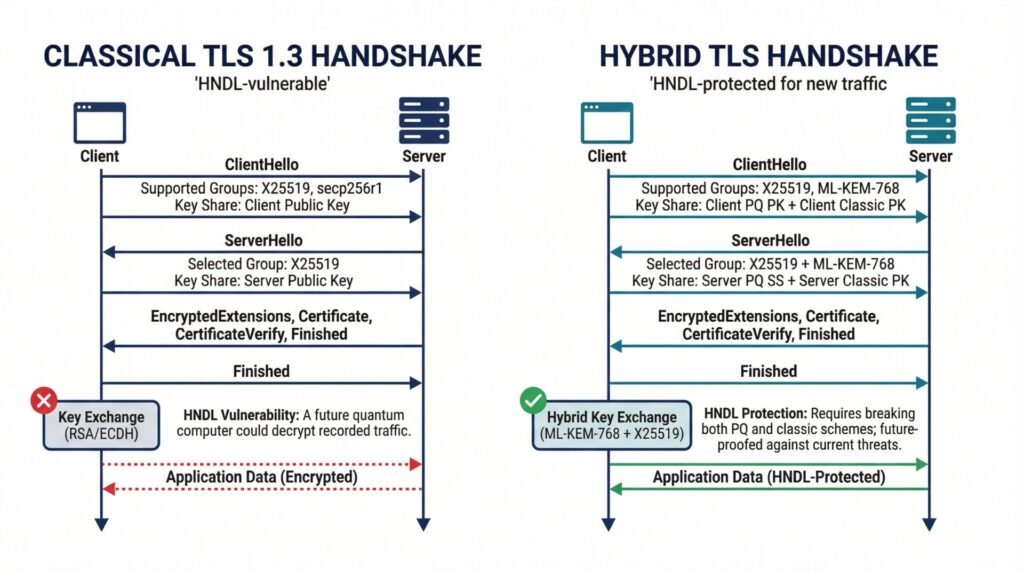
Phase 3 — Hybrid TLS Deployment: The Fastest HNDL Risk Reduction Available
Phase 3 is the highest-impact action available to most organizations in 2026. Deploying ML-KEM-768 + X25519 hybrid key exchange on all internet-facing TLS services immediately protects new traffic against HNDL collection — regardless of whether PKI migration (Phase 5) is complete. Cloudflare deployed this configuration across its global infrastructure, and by late 2025, over 50 percent of web traffic traversing Cloudflare’s network used hybrid post-quantum key exchange[7]. AWS, Google Cloud, and Microsoft Azure have all published hybrid TLS roadmaps and begun enabling ML-KEM configurations in their managed services.
The hybrid approach — formally designated X25519MLKEM768 — is supported natively in Chrome, Firefox, Edge, Brave, and Opera as of 2026[7]. CNSA 2.0 requires NSS web browsers and cloud services to support quantum-safe TLS by 2029 and for that to become exclusive by 2033[4]. For non-NSS enterprises, deploying hybrid TLS in 2026 provides immediate risk reduction while Phase 4 and Phase 5 work proceed in parallel. A full PQC migration of 2–5 years means that every quarter of delay during which internet-facing services remain on classical key exchange extends HNDL exposure for traffic that is already being collected.
Table 3: Cryptographic asset categories required in a complete Crypto Bill of Materials (CBOM) — examples and HNDL risk driver for each.
| Asset Category | Examples | HNDL Risk Driver |
| TLS certificates and web servers | Load balancers, CDN edge nodes, API gateways, HTTPS endpoints, web application servers | Internet-facing traffic is the primary HNDL harvesting target; the highest immediate exposure |
| VPN and network infrastructure | IPsec tunnels, SSL VPNs, network routers using IKEv2, and SD-WAN connections | Long-lived tunnels protecting sensitive communications; CNSA 2.0 requires migration by 2026–2030 |
| Code signing and firmware keys | CI/CD pipeline signing keys, firmware update signing, OS package signing, container image signing | Software supply chain integrity; CNSA 2.0 mandates PQC firmware signing support by 2025 |
| Certificate authorities and PKI | Root CAs, intermediate CAs, OCSP responders, CRL distribution points, HSMs | PKI chain longevity extends exposure across the entire certificate ecosystem |
| SSH keys and authentication | Server SSH host keys, developer authentication keys, jump host credentials, automated scripts | Long-lived SSH keys may already have been harvested; replacement prioritized by data sensitivity |
| Database encryption and key management | TDE keys, column encryption keys, backup encryption, KMS integrations | Data at rest with long retention periods carries direct HNDL exposure |
| Third-party and vendor dependencies | SaaS applications, cloud provider key exchange, API authentication, supply chain cryptography | 81% of organizations report cryptographic libraries not PQC-ready; vendor CBOM required |
Phase 5 — Post-Quantum PKI Migration Steps: The Longest and Most Complex Phase in a Post-Quantum Cryptography Migration Roadmap
Public Key Infrastructure migration is the most time-intensive phase of any post-quantum cryptography migration roadmap. Replacing RSA and ECDSA certificates across the full PKI chain — leaf certificates, intermediate CAs, and root CAs — requires coordination with certificate authorities, HSM vendors, browser and operating system ecosystems, and any application or device that validates X.509 certificate chains[9]. Certificate chains using ML-DSA-65 will be approximately 12 KB in total size versus 4 KB for RSA, a tripling that must be accounted for in bandwidth budgets, certificate pinning configurations, and TLS stack memory allocations.
NIST IR 8547 establishes that quantum-vulnerable algorithms will be deprecated from federal use by 2030 and disallowed entirely by 2035[10]. Within a structured post-quantum cryptography migration roadmap, PKI migrations at large enterprises historically take five to seven years to complete across the full certificate ecosystem[2]. This means that organizations not beginning PKI inventory and CA coordination in 2026 face a near-certain compliance gap against the 2030–2033 CNSA 2.0 and NIST deprecation milestones.
The first post-quantum cryptography migration roadmap certificates were piloted by DigiCert and others in 2026[9]. Organizations should engage their certificate authority on PQC roadmap availability, pilot ML-DSA certificates in non-production environments, and assess their HSMs for hybrid certificate support.
💡 For more information, explore the complete segments of our PQC Series
Counter-Arguments: Four Honest Challenges to the 6-Phase Roadmap
The most common failure pattern in post-quantum cryptography migration roadmap execution is not technical — it is organisational. Security teams that understand the urgency of the post-quantum cryptography migration roadmap frequently struggle to translate that urgency into a funded, governed programme with executive sponsorship. The four objections below are the ones most commonly encountered when presenting a migration roadmap to leadership, alongside the evidence-based responses that have proven most effective in moving organisations from awareness to action.
Objection: Our organization is too small for a formal 6-phase program — this level of structure is only appropriate for large enterprises.
Discussion: Migration complexity does scale with organizational size: large enterprises face 8–12 years of migration work under realistic assumptions, while small organizations with simpler infrastructure can complete migration in 5–7 years. [2] However, the CBOM inventory (Phase 1) and hybrid TLS deployment (Phase 3) are both achievable for organizations of any size, and both provide immediate HNDL risk reduction regardless of enterprise scale. The 2035 NIST deprecation deadline applies uniformly, and regulatory requirements under CNSA 2.0, NIS2, and DORA do not scale with organization size.
Solution: Apply the 6-phase framework proportionally to your scale. A small organization may complete Phases 1–3 in 12 months and compress Phases 4–5 substantially. The phases remain the correct logical sequence regardless of timeline compression.
Objection: The 2035 NIST deadline gives us nine years — there is no operational urgency to begin migration in 2026.
Discussion: This reasoning treats 2035 as a starting point rather than a completion milestone. NIST explicitly states that organizations should begin applying PQC standards now, not waiting for deadlines, because of enterprise migration complexity.[1] Full PQC migration at large enterprises takes 8–12 years under baseline assumptions, [2] meaning any organization beginning migration after 2027 faces a credible risk of non-compliance by 2035. The HNDL threat means that data encrypted today under RSA or ECC is already potentially in adversary archives — the 2035 deadline does not retroactively protect that data.
For organizations asking what to do about the NIST 2035 deprecation deadline now: the answer is to treat 2026 as the last responsible start date — not a comfortable midpoint.
Solution: Reframe the calendar: the last responsible start date for a complete migration is approximately 2026–2027 for organizations with complex infrastructure. Treat 2026 as the last window for a structured start, not the beginning of a comfortable countdown.
Objection: Phase 1 (cryptographic inventory) will take too long and consume too much budget before any actual security improvement is visible.
Discussion: The inventory is the prerequisite, not the entirety, of the program. NIST and NCCoE guidance explicitly separate the discovery workstream from the deployment workstream — both can run in parallel. [3] Automated cryptographic scanning tools, including IBM Quantum Safe Explorer and open-source CBOM tools based on the CycloneDX 1.6 standard, can produce an initial high-level inventory of internet-facing systems within weeks. Phase 3 (hybrid TLS deployment) can begin in parallel with detailed CBOM work — providing visible, measurable HNDL risk reduction before the full inventory is complete.
Solution: Separate the comprehensive CBOM effort (full enterprise discovery) from the initial risk-based scan (internet-facing systems first). Begin Phase 3 hybrid TLS deployment within 90 days of program initiation, using a preliminary inventory of the highest-exposure systems.
Objection: Cloud migration means our cryptography is the provider’s responsibility — our organization does not need its own migration roadmap.
Discussion: Cloud providers control the infrastructure layer — TLS between clients and cloud endpoints, key management services, and managed certificate authorities. However, applications running on cloud infrastructure still control their own cryptographic operations: application-level key generation, code signing pipelines, database encryption keys, and API authentication tokens. The NCCoE SP 1800-38 practice guide notes that cloud service endpoints must be included in enterprise CBOMs because organizations are responsible for cryptographic practices within their application layers, regardless of the infrastructure provider. [3] AWS, Azure, and Google Cloud have published PQC roadmaps, but their timelines do not automatically migrate customer application cryptography.
Solution: Request your cloud providers’ PQC roadmaps and confirm which cryptographic operations they manage versus which remain the organization’s responsibility. Include cloud API endpoints, managed certificate authorities, and KMS configurations in your CBOM as distinct asset categories.
Knowledge Assessment Quiz: Is Your PQC Migration on Track?
⚠ Disclaimer: This quiz is for self-awareness only and does not constitute a professional assessment.
Q1: Which Phase 1 output is the mandatory prerequisite for every subsequent phase of the migration roadmap?
- A) A completed hybrid TLS deployment on all internet-facing services
- B) A Crypto Bill of Materials (CBOM) mapping all quantum-vulnerable algorithm usage
- C) A signed executive authorization to begin PKI migration
- D) A vendor assessment report on HSM post-quantum readiness
Q2: An organization subject to CNSA 2.0 must ensure all new National Security Systems use quantum-safe key establishment by which deadline?
- A) December 31, 2035 — the full infrastructure migration deadline
- B) January 1, 2030 — the full application migration deadline
- C) January 1, 2027 — all new systems must use ML-KEM and ML-DSA
- D) August 13, 2024 — the NIST FIPS publication date
Q3: Why is PKI and certificate migration (Phase 5) the most complex and time-intensive phase of the roadmap?
- A) ML-DSA certificates are not yet approved by any certificate authority
- B) It requires coordination across CAs, browser vendors, HSM manufacturers, and the full PKI ecosystem
- C) PKI migration requires waiting for FN-DSA (FIPS 206) to finalize before ML-DSA can be deployed
- D) Certificate authorities are not permitted to issue hybrid certificates under the current NIST standards
Score Interpretation:
- All correct (B, C, B): Strong migration awareness. Use the 6-phase roadmap to build a board-level program plan with specific milestones and ownership.
- Mostly correct: Review Phase 1 (CBOM) and the CNSA 2.0 timeline — these are the two most operationally urgent elements for regulated organizations in 2026.
- Incorrect: Return to the regulatory compliance matrix in Table 2 and the phase descriptions before presenting a migration plan to leadership.
FAQ
Q1: Where does the 6-phase migration roadmap come from?
A: The 6-phase structure synthesizes guidance from NIST SP 1800-38 (the NCCoE Migration to Post-Quantum Cryptography practice guide), NIST CSWP 39 (Crypto Agility Strategies and Practices), the CNSA 2.0 compliance timeline, and current enterprise deployment experience documented by the Cloud Security Alliance.
The phases follow the logical dependency sequence: you cannot prioritize risk without an inventory; you cannot deploy hybrid TLS without knowing where TLS is used; you cannot migrate PKI without having tested hybrid certificates. The regulatory deadlines in the compliance matrix in Table 2 map each phase to its binding governance context.
Q2: What is a Crypto Bill of Materials (CBOM), and how is it different from a standard security inventory?
A: A CBOM is a structured catalog of every cryptographic asset across an organization — not just certificates and keys, but the algorithms, libraries, protocols, hardware modules, and vendor dependencies that implement cryptography.
Unlike a standard security inventory that identifies systems and applications, a CBOM records the specific cryptographic algorithms in use and classifies them by quantum vulnerability. The CycloneDX 1.6 standard now includes a CBOM format, and IBM Quantum Safe Explorer is among the automated tools that can generate CBOMs from application and infrastructure scanning.
Q3: How long does a typical enterprise PQC migration take?
A: Research published in late 2025 found that large enterprises face 8–12 years for full migration under baseline assumptions, medium enterprises 5–8 years, and small enterprises 3–5 years. These timelines reflect the full scope, including cryptographic inventory, hybrid deployment, application re-engineering, PKI migration, and hardware replacement cycles.
Phase 3 (hybrid TLS deployment) is an exception — most organizations can complete this for internet-facing services within 3–12 months. The longest phase is PKI migration, which historically requires five to seven years at large enterprises due to ecosystem coordination requirements.
Q4: What is the difference between the NIST 2035 deprecation deadline and the CNSA 2.0 deadlines?
A: NIST IR 8547 sets 2035 as the deadline for disallowing all quantum-vulnerable public-key algorithms in U.S. federal systems — this applies to all FISMA-regulated organizations.
CNSA 2.0 applies specifically to National Security Systems and is more aggressive: new systems must use ML-KEM and ML-DSA by January 2027, full application migration by 2030, and complete infrastructure migration by 2035. Organizations subject to CNSA 2.0 — including NSS operators and defense contractors — face binding milestones from 2025 onward, making their Phase 1–3 completion timeline effectively immediate.
Q5: Can Phase 3 (hybrid TLS) and Phase 4 (crypto-agility engineering) run in parallel?
A: Yes — parallel execution is the recommended approach. Hybrid TLS deployment on internet-facing services (Phase 3) does not depend on crypto-agility re-engineering (Phase 4); it can proceed immediately using existing TLS stack configurations.
Phase 4 is a longer-horizon architectural program that ensures new systems built from 2026 onward do not create future migration debt. Running both phases simultaneously optimizes the total program timeline — Phase 3 delivers immediate HNDL risk reduction while Phase 4 prevents the problem from compounding in new systems.
Q6: Which vendor and regulatory resources are most useful for Phase 1 cryptographic inventory?
A: NIST SP 1800-38B (Quantum Readiness: Cryptographic Discovery) provides detailed tooling guidance and test scenarios for automated discovery. IBM Quantum Safe Explorer and Keyfactor’s certificate management platform are among the enterprise tools that support CBOM generation. NIST CSWP 39 provides architectural guidance for building crypto-agility into the inventory and governance framework. For regulatory alignment, the Palo Alto Networks PQC standards guide consolidates the CNSA 2.0, NIST IR 8547, and international framework requirements in a single reference.
PQC Series Overview
This article is part of the Post-Quantum Security Series — a technical collection of guides exploring cryptographic vulnerabilities exposed by quantum computing, migration strategies for organizations, and the steps required to protect sensitive data before quantum decryption becomes operationally viable.
References
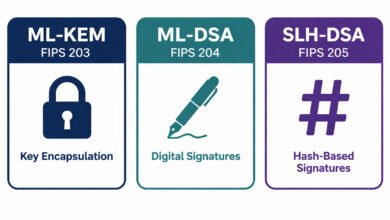
- [1] NIST. Post-Quantum Cryptography FIPS Approved — FIPS 203, 204, 205. August 13, 2024. https://csrc.nist.gov/news/2024/postquantum-cryptography-fips-approved
- [2] Cloud Security Alliance. Q-Day Clock: Enterprise Post-Quantum Migration Imperative. March 2026.
https://labs.cloudsecurityalliance.org/research/strategic-post-quantum-cryptography-migration-enterprise-roa/ - [3] NIST NCCoE. SP 1800-38B — Migration to Post-Quantum Cryptography: Cryptographic Discovery. December 2023:
https://www.nccoe.nist.gov/sites/default/files/2023-12/pqc-migration-nist-sp-1800-38b-preliminary-draft.pdf - [4] NSA. Commercial National Security Algorithm Suite 2.0 (CNSA 2.0). September 2022. https://www.nsa.gov/Press-Room/Press-Releases-Statements/Press-Release-View/article/3498776/
- [5] PQShield. PQC Transition Roadmaps and Global Framework Comparison. https://pqshield.com/resources/pqc-regulatory-landscape/
- [6] NIST. CSWP 39 — Considerations for Achieving Crypto Agility: Strategies and Practices. December 2025.
https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.39.pdf - [7] Cloudflare Research. NIST’s First Post-Quantum Standards — What This Means for the Internet. https://blog.cloudflare.com/nists-first-post-quantum-standards/
- [8] IBM Research. NIST’s Post-Quantum Cryptography Standards Are Here. August 2024. https://research.ibm.com/blog/nist-pqc-standards
- [9] DigiCert. Tracking the Progress Toward Post-Quantum Cryptography. November 2024. https://www.digicert.com/blog/the-progress-toward-post-quantum-cryptography
- [10] NIST. IR 8547 — Transition to Post-Quantum Cryptography Standards. 2024. https://nvlpubs.nist.gov/nistpubs/ir/2024/NIST.IR.8547.ipd.pdf