Post-Quantum Cryptography (PQC) 2026: Why Your Encryption Strategy Must Change Now
The data your organisation encrypted this morning may already be in the hands of a nation-state adversary. Not because your encryption has failed — but because it may fail within the decade, once a sufficiently powerful quantum computer becomes capable of decrypting it. This is the Harvest Now, Decrypt Later (HNDL) threat model, and it is increasingly treated as a credible risk scenario rather than a theoretical one.
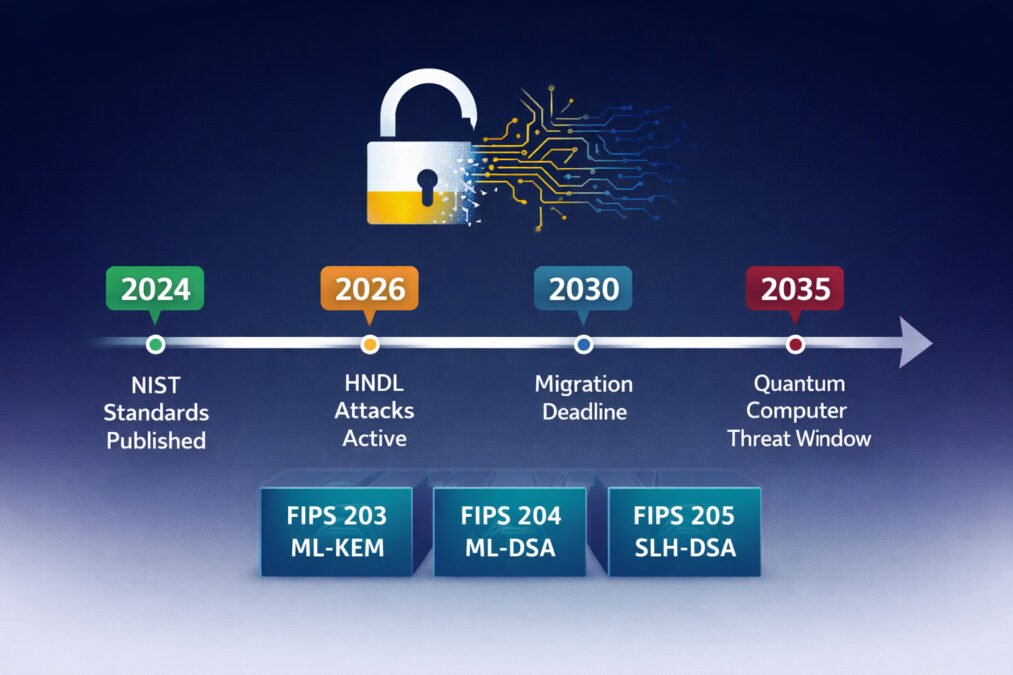
Post-Quantum Cryptography (PQC) 2026 is defined by a narrowing migration window. Evidence suggests that adversaries are likely conducting large-scale encrypted data collection aligned with HNDL strategies, while at the same time, standardised quantum-resistant algorithms are now available for deployment. The projected quantum threat window — often estimated between 2030 and 2040 — further compresses the time available for organisations to act.
The risk is asymmetric: attackers can wait — defenders cannot.
For organisations handling long-lived sensitive data — including healthcare records, financial contracts, legal communications, intellectual property, and government information — the effective security window is already shrinking. What was previously considered a future planning concern has become an immediate operational priority.
In August 2024, the National Institute of Standards and Technology (NIST) published the first three finalised post-quantum cryptography (PQC) standards, providing concrete and implementable algorithms for real-world use. At the same time, Michele Mosca’s framework highlights a critical constraint: when data longevity and migration timelines exceed the estimated arrival of quantum capability, the transition is already overdue.
This guide outlines the threat landscape, explains the new standards, and provides a structured six-step roadmap to support effective post-quantum cryptographic migration.
💡 For more information, explore the complete segments of our PQC Series
⚠ TECHNICAL DISCLAIMER This article is for educational and informational purposes only. It does not constitute professional cybersecurity, cryptographic, or legal advice. Cryptographic migration involves complex technical, regulatory, and operational dimensions. Organisations should engage qualified cryptography professionals and review applicable regulatory guidance before implementing cryptographic changes.
Why Post-Quantum Cryptography (PQC) Is Urgent in 2026 — Not in 2030
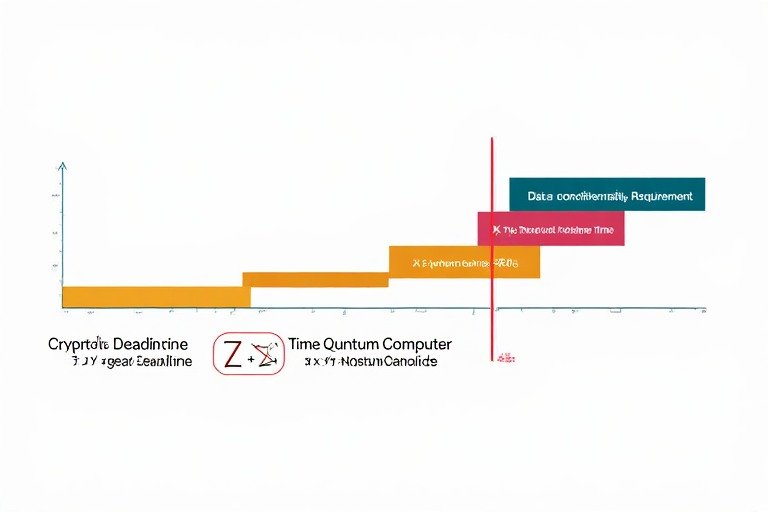
The most common misconception about post-quantum cryptography is temporal: organisations assume the threat is a decade away and the migration can wait. Mosca’s Theorem — named after cryptographer Michele Mosca — formalises why this assumption is dangerous. The theorem states that if X equals the number of years sensitive data must remain confidential, Y equals the time required to complete a cryptographic migration, and Z equals the years remaining before a cryptographically relevant quantum computer (CRQC) exists, then organisations must begin migration before X + Y exceeds Z.
In 2026, estimates vary widely, typically ranging from 10 to 20+ years depending on technological assumptions[2]. A healthcare record created today may require confidentiality for 30 years (X = 30). A cryptographic migration across a large enterprise may take 5–7 years (Y = 7). Applying Mosca’s Theorem: 30 + 7 = 37 years of required protection, against an estimated 5–15 years before the threat materialises.
This simplified example suggests that, for long-lived sensitive data, the optimal migration window may already have passed. The second-best time to begin is 2026. The quantum threat timeline makes delay quantifiably irresponsible for any organisation handling long-lived sensitive data.
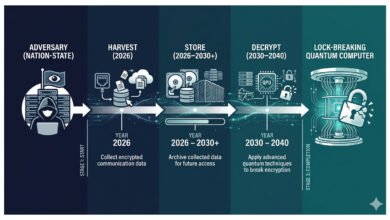
Harvest Now, Decrypt Later — The Threat That Is Already Happening
Harvest Now, Decrypt Later (HNDL) attacks operate on a simple and devastating logic: today’s encrypted traffic, captured and stored now, can be decrypted in the future when a CRQC becomes available. Sophisticated adversaries — primarily nation-state actors with the storage infrastructure and long-term strategic patience required — are already executing HNDL operations at scale. By late October 2025, Cloudflare reported rapid adoption of hybrid post-quantum key exchange, reflecting growing industry concern around potential HNDL risks.[3] Organisations that have not begun their post-quantum cryptography migration are actively generating data that adversaries are storing today.
Table 1: Post-Quantum Cryptography (PQC) 2026 — Threat and Readiness Landscape
| Metric | Status in 2026 | Source | Implication |
| NIST PQC standards published | Yes — FIPS 203, 204, 205 finalised Aug 2024 | NIST | Algorithms available for immediate deployment |
| HNDL attacks are likely occurring at scale | Yes — nation-states harvesting encrypted traffic now | Cloudflare / Medium 2026 | Urgency is present-tense, not future-tense |
| Quantum computer (CRQC) exists | No — does not exist as of 2026 | NIST / NIST CSRC 2026 | HNDL risk precedes CRQC arrival |
| Estimated CRQC arrival window | 2030–2040 (leading researcher consensus) | NIST / PQShield | Migration must be complete before the window opens |
| NIST deprecation deadline | 2035 — quantum-vulnerable algorithms deprecated | NIST IR 8547 | Regulatory compliance timeline now defined |
| Cloudflare PQ adoption | 50%+ of web traffic using PQ key exchange by late 2025 | Cloudflare Research | Major infrastructure is already transitioning |
| Enterprise PQC readiness | 81% report cryptographic libraries not ready for PQ [1] | Medium 2026 survey | The gap between urgency and readiness is large |
| CNSA 2.0 US Government mandate | NSM-10 sets 2035 target for federal systems | White House NSM-10 | Regulatory pressure is accelerating adoption |
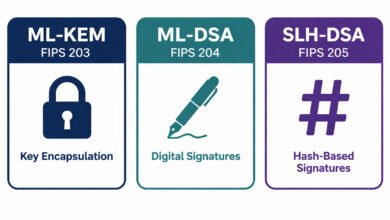
The Three NIST Post-Quantum Cryptography (PQC) Standards — What FIPS 203, 204, and 205 Mean
After an eight-year international standardisation process involving 82 submitted algorithms from 25 countries [4], NIST published three finalised post-quantum cryptography standards in August 2024. These algorithms are mathematically designed to resist attacks from both classical computers and quantum computers, using mathematical problems that quantum algorithms — including Shor’s algorithm, which would break RSA and ECC — cannot efficiently solve.
FIPS 203 — ML-KEM (Module-Lattice Key Encapsulation Mechanism)
ML-KEM, derived from the CRYSTALS-Kyber algorithm developed with IBM Research, is the primary quantum-safe encryption standard for key encapsulation — the mechanism used to establish shared secrets for encrypted communications. It replaces RSA and Elliptic Curve Diffie-Hellman (ECDH) in protocols including TLS, VPNs, and secure messaging. ML-KEM uses Module Learning With Errors (Module-LWE) mathematics, which has no known efficient quantum attack. Cloudflare has deployed ML-KEM + X25519 hybrid key exchange at internet scale — a model demonstrating that post-quantum cryptography is operationally viable in high-throughput production environments [3].
FIPS 204 — ML-DSA (Module-Lattice Digital Signature Algorithm)
ML-DSA, derived from CRYSTALS-Dilithium, provides quantum-safe digital signatures — the cryptographic mechanism used to verify the authenticity and integrity of software, documents, certificates, and communications. It replaces ECDSA and RSA-based signatures in code signing, certificate authorities, and authentication systems. ML-DSA adoption will take longer than ML-KEM due to the complexity of migrating Public Key Infrastructure (PKI) — the network of certificate authorities and trust anchors that underpins TLS, code signing, and email security globally.
FIPS 205 — SLH-DSA (Stateless Hash-Based Digital Signature Scheme)
SLH-DSA, derived from SPHINCS+, provides an alternative quantum-safe digital signature standard based on hash functions rather than lattice mathematics. Its mathematical security relies on properties of cryptographic hash functions that are well-understood and carry different risk assumptions than lattice-based approaches. NIST recommends SLH-DSA as a diversity hedge — if a weakness is discovered in lattice-based mathematics, hash-based signatures provide an independent fallback. Co-developed by a scientist now at IBM Research [4], SLH-DSA is best suited for use cases where slower performance and a larger bandwidth overhead are acceptable — its signature sizes are significantly larger than ML-DSA, making it optimal for low-frequency signing applications.
Table 2: NIST Post-Quantum Cryptography Standards — Comparison and Use Cases
| Standard | Algorithm Origin | Mathematical Basis | Primary Use Case | Replaces | Deployment Readiness |
| FIPS 203 — ML-KEM | CRYSTALS-Kyber (IBM Research) | Module Learning With Errors (MLWE) | Key encapsulation for encrypted communications | RSA, ECDH, DH | Available now — Cloudflare deployed at scale |
| FIPS 204 — ML-DSA | CRYSTALS-Dilithium (IBM Research) | Module Learning With Errors (MLWE) | General-purpose digital signatures | ECDSA, RSA signatures | Available — PKI migration complexity is high |
| FIPS 205 — SLH-DSA | SPHINCS+ (co-developed with IBM) | Hash-based cryptography | Backup signature standard, low-frequency signing | ECDSA (diversification hedge) | Available — larger signatures, lower speed |
| Hybrid: ML-KEM + X25519 | NIST-recommended interim approach | PQ + classical combination | TLS key exchange during the transition period | VPN / TLS key exchange | Recommended now — reduces risk during migration |
What Your Current Encryption Cannot Defend Against — The Quantum Vulnerability Map
Not all encryption is equally vulnerable to quantum attack. Understanding which cryptographic primitives are quantum-vulnerable and which are quantum-resistant is essential to prioritising a cryptographic migration correctly.
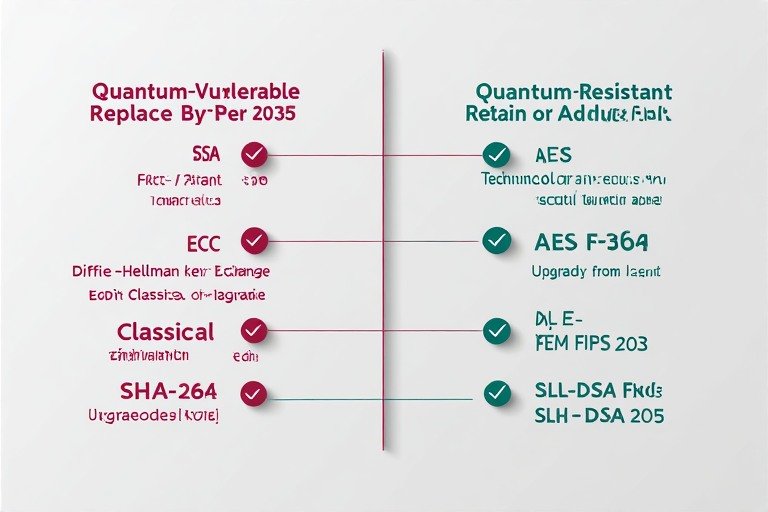
Quantum-Vulnerable Algorithms — Replace Before 2035
Shor’s algorithm — executable on a sufficiently powerful quantum computer — can efficiently solve the integer factorisation and discrete logarithm problems on which the following widely-deployed algorithms depend: RSA (all key sizes used in practice), Elliptic Curve Cryptography (ECC, ECDSA, ECDH), Diffie-Hellman key exchange, and the digital signature algorithms based on these primitives. These algorithms underpin TLS 1.3, most VPN implementations, PKI and certificate authorities, code signing systems, and SSH authentication. NIST IR 8547 establishes a 2035 deprecation deadline — but the HNDL threat means data with confidentiality requirements beyond 2035 is already exposed today [5].
Quantum-Resistant Algorithms — Retain With Key Length Adjustment
Symmetric encryption algorithms — AES, ChaCha20 — are not broken by Shor’s algorithm. Grover’s algorithm provides a quadratic speedup against symmetric keys, effectively halving their security level. AES-256 degrades to the security of AES-128 against a quantum adversary — still computationally infeasible to break, but organisations should migrate away from AES-128 toward AES-256 as part of their quantum readiness programme. Hash functions (SHA-256, SHA-3) face similar Grover’s algorithm degradation and should be migrated to SHA-384 or SHA-512 for long-lived applications.
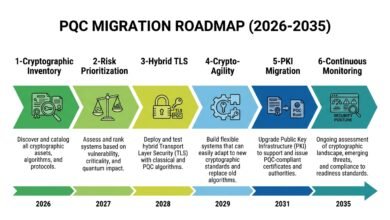
The 6-Step Post-Quantum Cryptography Migration Roadmap for 2026
The cryptographic migration to PQC in 2026 is a multi-year programme requiring systematic execution. The following six steps, informed by NIST SP 1800-38C and Palo Alto Networks’ PQC guidance[6], provide a sequenced roadmap applicable to organisations of most sizes and sectors.
Step 1 — How to Start PQC Migration: Conduct a Cryptographic Inventory
Identify every cryptographic implementation across your environment: TLS certificates, VPN configurations, code signing keys, SSH keys, database encryption, API authentication, hardware security modules (HSMs), and embedded device firmware.
This cryptographic inventory — sometimes called a Crypto Bill of Materials (CBOM) — is the prerequisite for all subsequent migration decisions. 81% of surveyed organisations reported that their cryptographic libraries and HSMs were not ready for PQ integration in 2026 [1] — making inventory the most urgent immediate action.
Step 2 — Prioritise by Data Sensitivity and Longevity
Not all cryptographic implementations carry equal HNDL risk. Prioritise migration for: data with confidentiality requirements beyond 2030 (healthcare records, legal contracts, financial archives, intellectual property), internet-facing TLS implementations exposed to traffic harvesting, long-lived certificates and signing keys, and government-regulated data subject to CNSA 2.0 or NSM-10 mandates. Low-priority migration targets include short-lived session keys and data with confidentiality requirements under three years.
Step 3 — Deploy Hybrid Cryptography for Immediate HNDL Risk Reduction
Hybrid cryptography — combining a quantum-vulnerable algorithm with a quantum-safe algorithm in parallel — provides immediate HNDL risk reduction while maintaining backwards compatibility. NIST permits hybrid key exchange using ML-KEM + X25519, and this combination is already deployed by Cloudflare and Google at internet scale.
The hybrid approach allows organisations to begin capturing quantum-safe encryption benefits in production without waiting for full PKI migration. Palo Alto Networks specifically recommends beginning with hybrid TLS deployments, noting that this is low-risk and should start immediately [6].
Step 4 — Achieve Crypto-Agility in New System Designs
Crypto-agility — the architectural property of being able to swap cryptographic algorithms without rewriting application logic — is the most strategically important engineering discipline of 2026. Systems built with hardcoded cryptographic algorithms will require full re-engineering rather than configuration updates when migration deadlines arrive.
NIST SP 800-131A Rev. 3 recommends designing all new systems to support cryptographic algorithm substitution as a standard architectural requirement. Legacy systems that cannot be redesigned should be scheduled for replacement and governed through compensating controls until migration is complete.
Step 5 — Migrate PKI and Certificate Infrastructure
Public Key Infrastructure migration — replacing the RSA and ECDSA-based certificates that underpin TLS, code signing, email authentication, and device identity — is the most complex and longest-duration phase of post-quantum cryptography transition. It requires coordination with certificate authorities, browser and operating system vendors, and hardware security module manufacturers. The first post-quantum certificates are expected to be available in 2026, but not enabled by default [3]. Organisations should begin PKI inventory, engage their certificate authority on PQC roadmap availability, and pilot ML-DSA certificates in non-production environments.
Step 6 — Validate, Monitor, and Maintain Crypto-Agility
Quantum-safe transition is not a one-time migration — it is an ongoing operational discipline. Cryptographic algorithms age: new weaknesses may be discovered in lattice-based mathematics, requiring rapid migration to backup algorithms such as SLH-DSA. Continuous cryptographic monitoring — automated scanning for quantum-vulnerable algorithm usage, certificate expiry tracking, and algorithm compliance reporting — provides the operational visibility required to maintain quantum readiness as the threat landscape evolves toward the 2035 deprecation deadline.
Table 3: Post-Quantum Cryptography 2026 — Migration Roadmap by Phase and Priority
| Phase | Timeline | Key Actions | HNDL Risk Reduction | Regulatory Alignment |
| Cryptographic Inventory | 0–3 months | CBOM creation, vulnerability mapping, and HSM assessment | Identifies highest-risk exposures | Foundation for NIST IR 8547 compliance |
| Prioritisation and Planning | 1–3 months | Risk-based migration sequencing, hybrid TLS pilot | Plans risk reduction sequence | CNSA 2.0 / NSM-10 alignment begins |
| Hybrid Deployment | 3–12 months | ML-KEM + X25519 TLS, VPN hybrid migration | Immediate — active traffic protected | NIST SP 800-56C Rev. 2 compliant |
| Crypto-Agility Engineering | 6–24 months | New systems built algorithm-agnostic | Prevents future migration debt | NIST SP 800-131A Rev. 3 aligned |
| PKI Migration | 12–36 months | PQC certificates, ML-DSA rollout, CA coordination | Eliminates signature vulnerability | FIPS 204 compliance achieved |
| Continuous Monitoring | Ongoing | Automated crypto scanning, algorithm compliance reporting | Maintains posture as algorithms evolve | 2035 deprecation deadline maintained |
Counter-Arguments: Four Honest Challenges to Post-Quantum Cryptography Urgency
A rigorous discussion of the current (PQC) landscape must engage directly with the strongest objections to the prevailing urgency narrative. These challenges are not merely theoretical; they reflect practical concerns around timing, feasibility, security assurance, and system performance.
One central objection questions whether PQC is truly urgent, given that large-scale quantum computers capable of breaking current cryptographic systems do not yet exist. This perspective assumes that action can be deferred until the threat becomes tangible. However, this reasoning overlooks the “harvest now, decrypt later” (HNDL) threat model, in which adversaries—particularly nation-states—are already collecting encrypted data with the intention of decrypting it once quantum capabilities mature.
As a result, urgency must be understood in present-tense terms rather than as a distant future concern. For organisations managing data that must remain confidential beyond 2030—such as in healthcare, legal, financial, and government sectors—the effective security window is already narrowing. That said, the level of urgency is not uniform: organisations dealing with short-lived data and minimal regulatory exposure face a lower immediate risk. Frameworks such as Mosca’s Theorem help quantify this urgency by balancing data longevity, migration complexity, and projected quantum timelines.
A second challenge concerns the practicality of meeting migration deadlines, particularly the 2035 target set by standards bodies and governments. While this deadline is technically achievable, it is highly dependent on when organisations begin their transition. Those initiating structured PQC programmes around 2026 are in a viable position to complete migration on time. In contrast, delays beyond 2027 significantly increase execution risk.
The most complex and time-intensive component is the migration of Public Key Infrastructure (PKI), which requires coordination across certificate authorities, browser ecosystems, and hardware vendors. Historical precedent suggests that such transformations can take five to seven years in large enterprises. Importantly, policy frameworks such as CNSA 2.0 and the White House NSM-10 define 2035 as a completion milestone, not a starting point. Current data indicating that 81% of organisations are not yet PQ-ready [1] highlights how early most are in this transition.
A third objection raises concerns about the security of the newly standardised PQC algorithms. Skeptics point out that no cryptographic system can be proven unconditionally secure, and that newly adopted algorithms may still harbor undiscovered weaknesses. This concern is valid in principle and reflects a fundamental limitation of cryptography. However, the NIST-standardised algorithms—ML-KEM, ML-DSA, and SLH-DSA—have undergone an extensive eight-year international evaluation involving hundreds of experts across more than two dozen countries.
As of 2026, no practical vulnerabilities have been identified. Moreover, NIST’s strategy explicitly incorporates algorithmic diversity by recommending both lattice-based and hash-based approaches. This diversification ensures that if a weakness emerges in one mathematical domain, alternative constructions remain secure. Hybrid deployment models further mitigate risk by maintaining classical cryptographic protections during the transition period.
Finally, performance overhead is often cited as a barrier to adoption. Post-quantum algorithms, particularly ML-DSA and SLH-DSA, generate larger signatures and may impose additional computational costs compared to classical schemes.
This is a legitimate engineering consideration, especially in high-performance or resource-constrained environments. However, real-world deployments suggest that these challenges are manageable. For example, ML-KEM has demonstrated acceptable performance at internet scale, with large providers successfully deploying hybrid key exchange mechanisms across substantial portions of global web traffic. Industry guidance, including recommendations from major cybersecurity firms, supports immediate TLS migration on the basis that performance characteristics are sufficiently mature for most applications. Constraints remain more pronounced in IoT and embedded systems, where limited processing power and memory require hardware-accelerated PQC solutions. These are increasingly available in newer generations of secure hardware, providing a viable path forward for constrained environments.
In summary, while the objections to PQC urgency are grounded in legitimate concerns, they do not negate the underlying need for timely action. Instead, they refine the conversation—shifting it from whether to act, to how and when to act effectively based on organisational context.
The real risk is not that quantum computers arrive earlier than expected — but that organisations underestimate the time required to adapt
KNOWLEDGE ASSESSMENT QUIZ: How Quantum-Ready Is Your Organisation in 2026?
Post-Quantum Cryptography Readiness Disclaimer: This quiz is for self-awareness only and does not constitute a clinical assessment, security audit, or professional recommendation.
Q1: Has your organisation conducted a cryptographic inventory identifying all RSA, ECC, and Diffie-Hellman implementations?
A) Yes — full CBOM complete with risk prioritisation by data sensitivity
B) Partial — major systems identified but not comprehensively inventoried
C) No formal cryptographic inventory has been conducted
D) We do not know where cryptography is used across our environment.
Q2: Does your organisation’s TLS implementation support hybrid post-quantum key exchange (ML-KEM + X25519)?
A) Yes — hybrid PQC key exchange already deployed in production
B) In progress — testing hybrid deployment in non-production environments
C) Planned — on the roadmap but not yet started
D) No — TLS implementation has not been assessed for PQC readiness.
Q3: Are new systems and applications your organisation builds designed with crypto-agility — the ability to swap algorithms without rewriting logic?
A) Yes — crypto-agility is a standard architectural requirement for all new systems
B) Partially — some teams follow this practice, but it is not an organisation-wide policy
C) No — cryptographic algorithms are hardcoded in our applications
D) We have not assessed our crypto-agility posture.
Q4: Has your organisation mapped which data assets face the highest Harvest Now, Decrypt Later risk based on confidentiality lifetime?
A) Yes — HNDL risk mapped and migration priority established for high-risk data
B) Awareness exists, but no formal HNDL risk mapping has been completed
C) No — HNDL risk has not been formally assessed
D) We are not aware of the Harvest Now, Decrypt Later threat model.
Q5: Is your organisation’s Quantum-safe transition formally included in your security roadmap with
assigned ownership and a target completion date?
A) Yes — formal PQC programme with ownership, budget, and 2030–2035 completion target
B) Informally discussed but not yet a funded programme
C) No formal programme exists
D) Post-quantum cryptography has not been raised at the leadership level.
Score Interpretation:
Mostly A: Your organisation demonstrates strong quantum readiness. Focus on PKI migration planning, SLH-DSA backup algorithm deployment, and supply chain CBOM requirements.
Mostly B: Awareness is present, but structured action is missing. Formalise a PQC programme with ownership, begin hybrid TLS deployment, and complete a cryptographic inventory.
Mostly C/D: Significant HNDL exposure exists, and migration complexity will grow with each year of delay. Engage a qualified cryptography professional immediately to begin a structured Current PQC landscape assessment.
Final Thoughts
Post-quantum cryptography 2026 occupies a unique position in the cybersecurity threat landscape: it is the only major threat category where the attack has not yet fully arrived but where the defensive action must begin immediately to be effective when it does.
The Harvest Now, Decrypt Later threat model means that data exposed today cannot be retroactively protected by future migration. The migration window defined by Mosca’s Theorem is narrowing. The NIST standards — FIPS 203, 204, and 205 — are published, vetted, and ready for deployment.
The practical starting point for every organisation is the same: conduct a cryptographic inventory, identify the data assets that carry the highest HNDL exposure, and begin hybrid TLS deployment as an immediate risk reduction measure. PKI migration, crypto-agility engineering, and continuous monitoring follow in sequence. None of these steps requires waiting for quantum computers to arrive. All of them require organisational commitment to begin in 2026, not 2030. The organisations that complete their quantum-safe encryption migration before the CRQC arrives will have protected their data. Those who delay will face the consequences of inaction.
FAQ
Q1: What is post-quantum cryptography, and how is it different from current encryption?
A: Post-quantum cryptography refers to cryptographic algorithms that are mathematically resistant to attacks from quantum computers — specifically Shor’s algorithm, which can efficiently break RSA and ECC-based encryption currently in widespread use. Current encryption relies on the computational difficulty of factoring large numbers or solving discrete logarithm problems — problems that classical computers cannot solve but quantum computers can.
Post-quantum algorithms use mathematical structures — primarily lattice-based and hash-based mathematics — that have no known efficient quantum attack. NIST published the first three finalised standards (FIPS 203, 204, 205) in August 2024, providing organisations with concrete deployment targets.
Q2: What is Harvest Now, Decrypt Later, and is it actually happening?
A: Harvest Now, Decrypt Later is a threat model where adversaries collect and store encrypted communications today, intending to decrypt them once a cryptographically relevant quantum computer becomes available.
By early 2026, leading security researchers and infrastructure providers, including Cloudflare, indicate increasing concern around HNDL-style data collection operations — harvesting encrypted internet traffic at scale. This is not speculative: Cloudflare’s deployment of quantum-safe encryption for key exchange was accelerated specifically in response to documented HNDL activity. The threat is present-tense, not future-tense.
Q3: Which of the three NIST post-quantum standards should our organisation deploy first?
A: For most organisations, ML-KEM (FIPS 203) should be deployed first as a hybrid key exchange alongside existing X25519 in TLS configurations. This delivers immediate HNDL risk reduction for internet-facing communications with the lowest implementation complexity.
Cloudflare and Google have demonstrated ML-KEM + X25519 hybrid at internet scale, confirming operational viability. ML-DSA (FIPS 204) follows for digital signature migration, beginning with non-production certificate environments. SLH-DSA (FIPS 205) should be assessed as a backup signature standard for systems requiring algorithmic diversity or low-frequency signing applications.
Q4: Does (PQC) migration affect system performance?
A: Performance impact varies by algorithm and use case. ML-KEM demonstrates acceptable performance at very high throughput — Cloudflare’s internet-scale deployment confirms this. ML-DSA and SLH-DSA produce larger signatures than their classical counterparts, introducing a modest performance overhead in signature-intensive workflows. For constrained IoT and embedded devices, hardware-accelerated PQC implementations in the 2025–2026 generation secure elements significantly reduce the performance gap.
The recommendation from NIST and Palo Alto Networks is to begin with TLS hybrid deployment now — the performance characteristics are well-characterised and acceptable for the vast majority of enterprise use cases.
Q5: What is the 2035 NIST deadline, and what happens if we miss it?
A: NIST IR 8547 establishes 2035 as the target date for deprecating quantum-vulnerable classical algorithms — specifically RSA and ECC-based cryptography — across US federal systems and, by extension, across the broader ecosystem.
Missing this deadline does not mean encryption immediately fails — it means operating with algorithms that may be breakable by an adversary with quantum capability. The practical consequence depends on whether a cryptographically relevant quantum computer exists by 2035, which remains uncertain. However, the HNDL exposure for data encrypted before migration is not resolved by meeting the 2035 deadline — only by protecting data before it is harvested. This reinforces why beginning migration in 2026 is more valuable than meeting the 2035 deadline alone.
Q6: How does the current PQC landscape migration relate to regulatory compliance?
A: Multiple regulatory frameworks now explicitly reference the current PQC landscape requirements. The White House NSM-10 National Security Memorandum mandates transition for US national security systems by 2035. CNSA 2.0 provides specific algorithm requirements for US national security systems with earlier migration windows.
The EU’s NIS2 and DORA frameworks reference cryptographic resilience requirements that align with PQC migration priorities. NIST IR 8547 provides the definitive algorithm deprecation timeline applicable to FISMA-regulated organisations. Organisations in regulated industries should review these frameworks in conjunction with qualified legal and cryptographic counsel to establish their specific compliance obligations.
PQC Series Overview
This article is part of the Post-Quantum Security Series — a technical collection of guides exploring cryptographic vulnerabilities exposed by quantum computing, migration strategies for organizations, and the steps required to protect sensitive data before quantum decryption becomes operationally viable.
References
- [1] Deloitte: Quantum Readiness Survey 2025. https://www2.deloitte.com/us/en/pages/risk/articles/quantum-readiness.html
- [2] NIST: Getting Ready for Post-Quantum Cryptography.
- https://csrc.nist.gov/projects/post-quantum-cryptography
- [3] Cloudflare Research. NIST’s First Post-Quantum Standards — What This Means for the Internet. https://blog.cloudflare.com/nists-first-post-quantum-standards/
- [4] IBM Research. NIST’s Post-Quantum Cryptography Standards Are Here. https://research.ibm.com/blog/nist-pqc-standards
- [5] NIST. IR 8547 (ipd) — Transition to Post-Quantum Cryptography Standards. https://nvlpubs.nist.gov/nistpubs/ir/2024/NIST.IR.8547.ipd.pdf
- [6] Palo Alto Networks. A Complete Guide to Post-Quantum Cryptography Standards. https://www.paloaltonetworks.com/cyberpedia/pqc-standards