Zero Trust Architecture 2026: The Essential Implementation Guide for IT Teams
Your VPN was breached last quarter. Your attackers spent 21 days inside your network before anyone noticed. They moved laterally from a compromised contractor account to your customer database without triggering a single alert. If this scenario sounds familiar, it is because it reflects the majority of significant breaches documented in the IBM X-Force Threat Intelligence Index — and every one of them was preventable with Zero Trust architecture.
⚠ TECHNICAL DISCLAIMER This article is for educational and informational purposes only. It does not constitute professional cybersecurity advice, a security audit, or a specific product recommendation. Organisations should engage qualified cybersecurity professionals before implementing architectural or policy changes. Zero Trust implementation timelines, costs, and outcomes vary significantly by organisation size, existing architecture, and resource availability.
In 2026, Zero Trust architecture has moved from a conceptual framework to an operational imperative. 81% of organisations are actively implementing Zero Trust strategies. The market is valued at $48.43 billion this year and growing at 16% annually. Organisations that have deployed it report 50% lower breach impact costs and 83% faster incident response times [2][5]. This guide provides the complete six-step implementation framework, the evidence base that justifies the investment, and the practical guidance that most implementation resources omit.
Why Zero Trust Architecture Is Non-Negotiable in 2026
The business case for Zero Trust architecture in 2026 is no longer built on theory. It is built on documented, quantified breach economics. The perimeter-based security model was built on a simple assumption: trust everything inside the network and block everything outside. It was designed for an era of fixed offices, on-premises servers, and a defined boundary between internal and external.
The average enterprise now operates across more than 100 SaaS applications [1]. 56% of organisations reported VPN-exploited breaches last year — a significant rise from the prior period [6].
Human factors contributed to 68% of all incidents, and third-party weaknesses climbed 68% in a single year [2]. Each of these statistics reflects a world in which the perimeter is meaningless: the threat is already inside, operating through legitimate credentials, exploiting implicit trust. The foundational principle of Zero Trust — never trust, always verify — directly addresses these attack vectors.
The Market and Regulatory Momentum
Adoption is no longer voluntary in many sectors. The US Executive Order 14028 mandated Zero Trust architecture across all federal agencies.
The EU NIS2 Directive and DORA regulation require continuous verification and access control disciplines that are architecturally inseparable from Zero Trust principles. Gartner projects that 60% of large enterprises will have implemented measurable Zero Trust programmes by the end of 2026, up from less than 10% in 2023 [3].
According to market research estimates, the Zero Trust architecture market reached approximately $48 billion in 2026, with forecasts projecting growth past $100 billion by 2031 [4].
Table 1: Zero Trust Architecture vs Legacy Perimeter Security — 2026 Comparative Analysis
| Security Dimension | Legacy Perimeter Model | Zero Trust Architecture 2026 | Business Impact |
| Trust Model | Implicit trust inside the network | Never trust, always verify every request | Eliminates lateral movement after initial breach |
| Identity Verification | Single sign-on at network entry | Continuous adaptive re-authentication | Reduces credential theft impact by 50%+ |
| Remote Access | VPN — broad network access | ZTNA — application-specific, least-privilege | 56% fewer VPN-exploited breaches [6]. |
| Threat Containment | Perimeter blocks external threats | Micro-segmentation limits blast radius | 83% faster incident response times |
| Visibility | Network-level monitoring | Full session telemetry across all layers | 98-day faster breach containment (IBM) [8]. |
| Compliance | Point-in-time audit posture | Continuous policy enforcement | Satisfies NIS2, DORA, and NIST CSF 2.0 requirements |
| Cost | Lower upfront — higher breach cost | $48.4B market — lower post-breach cost | 50% reduction in breach impact cost (IBM) |
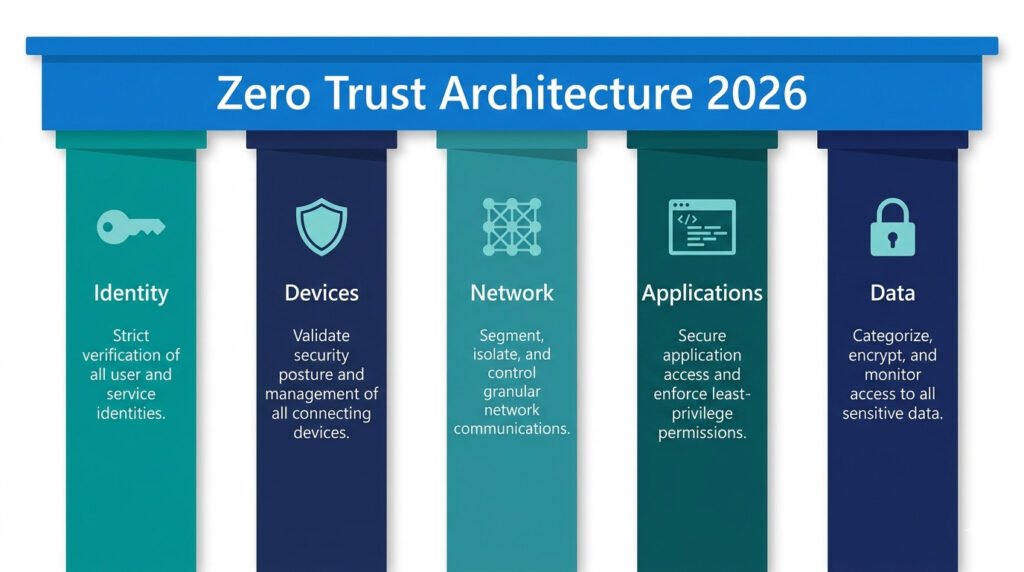
The Five Pillars of Zero Trust Architecture in 2026
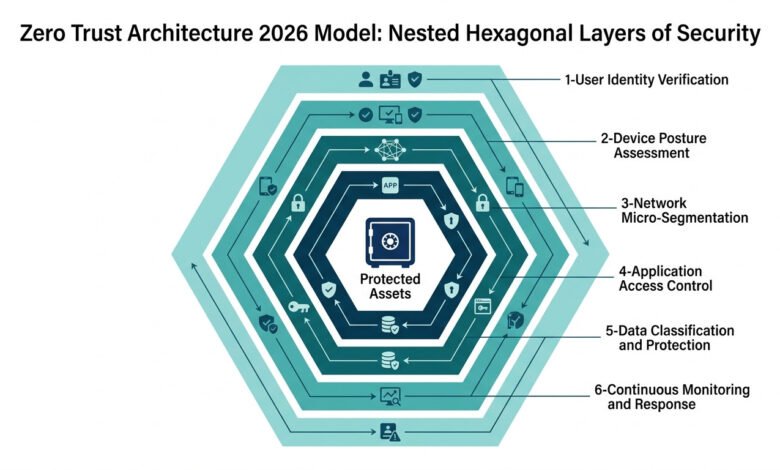
NIST Special Publication 800-207 defines Zero Trust architecture across five foundational pillars. Each pillar represents an independent control domain that must be addressed for a Zero Trust programme to achieve its designed security outcomes. Partial implementation leaves exploitable trust gaps that adversaries can target.
Pillar 1 — Identity: The New Perimeter
78% of Zero Trust initiatives begin with identity and access management modernisation [6] — and for good reason. Identity is the most-exploited attack surface in the current threat landscape. IBM X-Force identifies credential abuse as a consistently dominant initial access vector. The identity pillar encompasses phishing-resistant MFA, just-in-time privileged access, non-human identity governance, and adaptive authentication that responds to real-time risk signals.
The 2026 extension of this pillar is non-human identity governance: service accounts, API tokens, OAuth grants, and AI agent credentials now outnumber human identities in most enterprise environments and represent the largest under-governed attack surface. Extending Zero Trust identity controls to every identity — human and non-human — is the defining identity security mandate of 2026.
Pillar 2 — Devices: Continuous Posture Assessment
Zero Trust for devices operates on the principle that a device’s trustworthiness is not binary; it must be continuously evaluated. A device that was compliant at 9 a.m. may be compromised by 11 a.m. Device posture assessment evaluates patch level, configuration compliance, endpoint detection and response (EDR) status, and behavioural anomalies in real time, granting access only to devices that maintain a defined compliance threshold at the moment of each access request.
Pillar 3 — Network: Micro-Segmentation Replaces the Flat Network
The flat network — where a single compromised credential provides access to the entire internal environment — is the primary enabler of lateral movement in the 21-day average dwell time breaches documented by IBM and Mandiant.
Micro-segmentation divides the network into discrete segments, each with its own access controls, such that a compromise of one segment cannot propagate to adjacent systems without re-authentication and re-authorisation. This is the architectural control that reduces the blast radius of an inevitable breach from catastrophic to contained.
Pillar 4 — Applications: Least-Privilege Access to Every Workload
The principle of least privilege governs application access in a Zero Trust model: every user, every device, and every service receives only the access required for a specific task, for a specific duration, with continuous validation throughout the session. ZTNA replaces broad VPN access with application-specific, per-session connections that are individually verified, terminate automatically when the session ends, and are logged in full for audit and analysis.
Pillar 5 — Data: Classification, Encryption, and Access Governance
Data is the ultimate target of virtually every attack in the Zero Trust architecture threat model. The data pillar addresses classification (what data exists and where), encryption (data encrypted at rest and in transit by default), and access governance (who can access which data, under what conditions, with what audit trail). In 2026, this pillar has expanded to encompass AI-generated data and the outputs of AI workloads — a new data category with distinct classification and governance requirements.
💡 For more information, explore the complete segments of our AI Threats Security Series.
The Zero Trust Architecture 2026 Implementation Guide — Six Essential Steps
A full Zero Trust implementation typically takes 18–36 months for large enterprises [1]. The following six steps, sequenced by impact and dependency, provide a practical roadmap applicable to organisations of most sizes. Each step builds the foundation for the next — skipping steps or implementing out of sequence creates architectural gaps that adversaries will exploit.
Step 1 — Define Your Protect Surface
Before deploying any Zero Trust control, map what you are protecting. The protected surface — the most critical data, applications, assets, and services (DAAS) — is far smaller and more manageable than the total attack surface. Identifying your protected surface with precision allows you to apply the most rigorous controls where they matter most, rather than attempting to apply uniform controls everywhere simultaneously. This step produces an inventory of crown-jewel assets that drives every subsequent architectural decision.
Step 2 — Map Transaction Flows
Document how traffic flows to and from your protected surface: which users access which applications, from which devices, under which conditions, with which intermediate systems. Transaction flow mapping exposes implicit trust relationships — the service-to-service connections, API integrations, and automated workflows that are rarely documented and frequently over-privileged. These undocumented trust relationships are where sophisticated adversaries establish persistence after initial compromise.
Step 3 — Architect Zero Trust for the Protect Surface
Deploy a segmentation gateway — whether a next-generation firewall, a ZTNA solution, or a cloud access security broker (CASB) — at the boundary of the protected surface. This gateway enforces micro-segmentation, inspects all traffic traversing the boundary, and implements layer 7 access controls based on identity, device posture, and application context. This is the control that transforms the conceptual Zero Trust principle into an operational network architecture.
Step 4 — Create Zero Trust Policy
Zero Trust policy answers the Kipling question: who is requesting access, which application they are accessing, when they are accessing it, where they are accessing it from, why they need access, and how they are connecting. Policies are expressed as access rules enforced by the segmentation gateway. The starting point for all policies is deny-all with explicit grant — the inverse of the legacy allow-all with explicit deny model that characterises most legacy firewall configurations.
Step 5 — Monitor and Maintain
Zero Trust is not a deployment — it is a continuous operational practice. Continuous verification security requires telemetry from all five pillars, aggregated into a security information and event management (SIEM) or extended detection and response (XDR) platform, with AI-powered behavioural analytics to identify anomalies that rule-based systems miss. Security Week’s 2026 analysis confirms: organisations that treat Zero Trust as a destination rather than a continuous practice fail to realise its security benefits within 18 months of deployment [5].
Step 6 — Extend to Non-Human Identities and AI Workloads
The final — and most frequently omitted — step in Zero Trust implementation is non-human identity governance within a Zero Trust framework. Service accounts, API integrations, CI/CD pipelines, and AI agent credentials must be subject to the same authentication, authorisation, and monitoring rigour as human accounts — yet in most organisations they remain entirely ungoverned, representing the fastest-growing attack surface in the enterprise environment.
Table 2: Zero Trust Architecture 2026 — Implementation Roadmap by Phase
| Phase | Timeline | Key Actions | Controls Deployed | Success Metric |
| Foundation | 0–3 months | Asset inventory, protect surface definition, IAM audit | MFA, identity governance, asset register | 100% MFA on privileged accounts |
| Identity First | 3–6 months | Deploy phishing-resistant MFA, PAM, adaptive auth | Hardware MFA, PAM platform, ZTNA pilot | Zero standing privileged access |
| Network Segmentation | 6–12 months | Micro-segmentation, ZTNA deployment, VPN replacement | ZTNA, segmentation gateway, EDR | VPN fully replaced for target workloads |
| Application Control | 9–18 months | App-level ZTNA, least-privilege policy enforcement | CASB, DLP, application gateway policies | All apps on the least-privilege access model |
| Data Governance | 12–24 months | Data classification, encryption, AI data governance | DLP, DSPM, encryption at rest/transit | All sensitive data is classified and encrypted |
| Continuous Operation | Ongoing | NHI governance, AI workload security, red team | AI-SPM, XDR, continuous monitoring | Mean dwell time under 24 hours |
Zero Trust Architecture for the Remote and Hybrid Workforce in 2026
The permanent establishment of hybrid work is one of the primary structural drivers of Zero Trust architecture adoption. 65% of organisations plan to replace VPN services within the year — a 23% jump from the prior period [6]. The reasons are straightforward: VPNs grant broad network access based on a single authentication event, creating an attack surface that AI-powered reconnaissance tools can probe continuously from the public internet.
Zero Trust for remote work operates on a fundamentally different model. Rather than establishing a trusted tunnel to the entire network, ZTNA establishes application-specific connections that are continuously verified against the user’s identity and device posture, are limited to the specific application being accessed, are terminated when the session ends, and are logged in full for subsequent analysis. The user experience is comparable to or faster than VPN — the security posture is categorically superior.
The SASE Convergence
Secure Access Service Edge (SASE) — the convergence of Zero Trust network access, secure web gateway, cloud access security broker, and SD-WAN into a unified cloud-delivered service — has emerged as the dominant architectural pattern for organisations deploying Zero Trust for remote work at scale. Gartner projects SASE adoption will continue to accelerate through 2026 as organisations seek to consolidate the point-solution complexity that has accumulated through years of incremental security tool acquisition.
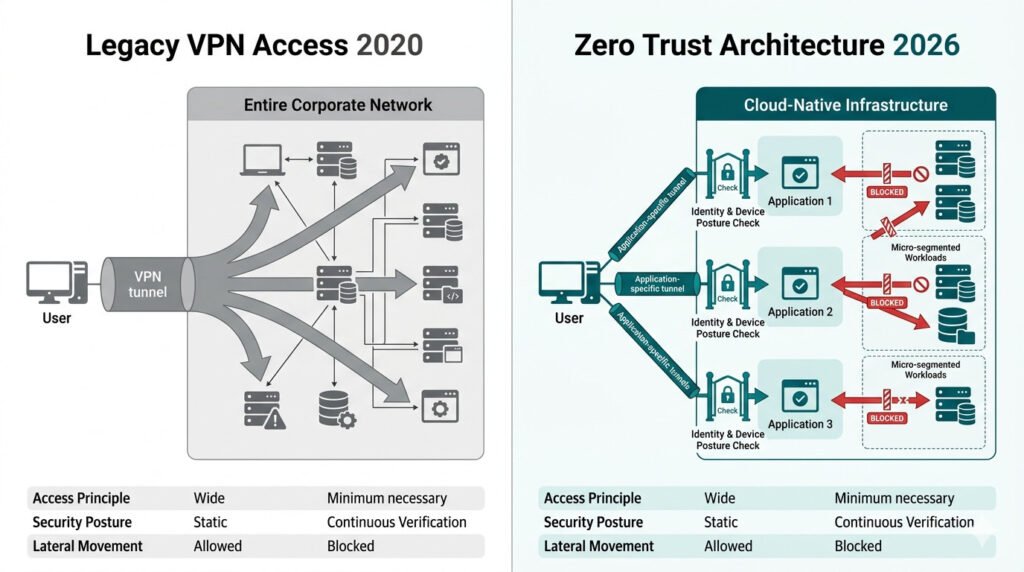
Table 3: Zero Trust Architecture 2026 — Key Vendor Capabilities by Pillar
| Pillar | Representative Vendors | Core Capability | Best Suited For |
| Identity | Microsoft Entra ID, Okta, CrowdStrike Falcon Identity | Adaptive MFA, PAM, NHI governance | All organisation sizes — cloud or hybrid |
| Devices | CrowdStrike Falcon, SentinelOne, Microsoft Intune | EDR, device posture, compliance enforcement | Organisations with managed endpoint fleets |
| Network (ZTNA) | Zscaler ZPA, Palo Alto Prisma SASE, Cloudflare Access | App-specific tunnels, micro-segmentation | Distributed/remote workforces, VPN replacement |
| Applications | Akamai EAA, Netskope, Cisco Duo | App-layer access control, CASB, DLP | SaaS-heavy environments, multi-cloud |
| Data | Microsoft Purview, Varonis, Rubrik | Data classification, DSPM, encryption | Regulated industries, high-value data environments |
| Monitoring (XDR) | Microsoft Sentinel, Splunk, IBM QRadar | SIEM/XDR, AI behavioural analytics, telemetry | Enterprise SOC teams, MDR programmes |
💡 For more information, explore the complete segments of our AI Threats Security Series.
Counter-Arguments: Four Honest Challenges to Zero Trust Adoption
A rigorous treatment of Zero Trust Architecture (ZTA) requires engaging with the legitimate architectural and operational hurdles that organisations face. Below is a discussion of the primary objections and the pragmatic realities of implementation in 2026.
1. The Resource Constraint Objection
The Challenge: There is a prevailing argument that Zero Trust is an “elite-only” architecture, practically unreachable for organisations lacking dedicated, high-tier security teams. Critics suggest that the complexity of full deployment creates a barrier to entry that only global enterprises can breach.
The Discussion: While enterprise-grade ZTA requires expertise, the shift toward cloud-delivered managed services has democratized access. Solutions from providers like Zscaler, Cloudflare, and Microsoft now offer Zero Trust as a Service (ZTaaS), requiring minimal on-premises infrastructure. In fact, the SMB segment is forecast to hold 60% of the ZTA market share over the next decade. This shift proves that by starting with identity—specifically, phishing-resistant MFA—measurable benefits are achievable at any budget tier without needing a massive in-house SOC.
2. The “Silver Bullet” Fallacy
The Challenge: Opponents often point to the high cost of Zero Trust by questioning its ultimate efficacy: Does it actually eliminate the risk of a breach, or is it merely an expensive mitigation layer? If a compromise can still occur, is the investment justified?
The Discussion: It is a fundamental reality that Zero Trust is a containment and visibility architecture, not a prevention panacea. By 2026, Gartner predicts that over half of cyberattacks will target areas where ZTA solutions do not mitigate risks [3]—such as social engineering and AI prompt injection. Zero Trust does not claim to block legitimate access used maliciously; rather, it drastically reduces the blast radius and dwell time. Organisations expecting total prevention will be disappointed; those seeking to limit the impact of an inevitable breach will find the evidence fully supportive.
3. The Legacy Infrastructure Barrier
The Challenge: A significant technical objection lies in the “Legacy Trap.” Critics argue that old on-premises systems simply cannot support modern authentication protocols or real-time telemetry, making a native Zero Trust retrofit virtually impossible.
The Discussion: Retrofitting Zero Trust into legacy systems is indeed rarely feasible. However, the pragmatic alternative is a hybrid migration. Instead of trying to force modern controls onto old hardware, architects should deploy Zero Trust controls at the perimeter of legacy environments. By using segmentation gateways to enforce least-privilege access, legacy dependencies can be shielded by modern environments. The goal is to control access to the legacy system through ZTA, even if the system itself remains technically “un-trusting.”
4. The Measurability Gap
The Challenge: From a management perspective, there is an objection regarding ROI. How can an organisation truly measure the success of a “Zero” state? Without clear metrics, Zero Trust can feel like an endless, unquantifiable project.
The Discussion: Success in Zero Trust is not a feeling; it is a metric. According to the IBM Cost of a Data Breach 2025, organisations with full ZTA deployment saw $2.2 million lower breach costs [8]. Performance can be quantified through four primary KPIs: MTTD (Detection Time), MTTR (Response Time), the Blast Radius (number of affected systems), and the reduction in Lateral Movement. When combined with annual red team assessments, these metrics provide the objective evidence required to prove the architecture is performing as designed under adversarial conditions.
KNOWLEDGE ASSESSMENT QUIZ:
How Mature Is Your Organisation’s Zero Trust Architecture?
Zero Trust Maturity Disclaimer: This quiz is for self-awareness only and does not constitute a clinical assessment, security audit, or professional recommendation.
Q1: Has your organisation replaced or begun replacing VPN with Zero Trust Network Access (ZTNA) for remote workforce access?
A) Yes — ZTNA fully deployed, VPN decommissioned or scheduled for decommission
B) In progress — ZTNA deployed for some workloads, VPN still primary
C) Planned — ZTNA is on the roadmap but not yet deployed
D) No plans — VPN remains the primary remote access solution.
Q2: Does your organisation enforce micro-segmentation — isolating critical systems so a compromise cannot spread laterally?
A) Yes — micro-segmentation deployed around all critical workloads
B) Partial — some network segments are isolated, not all critical systems
C) Basic — VLANs exist, but no granular micro-segmentation
D) No — flat network architecture with broad internal access
Q3: Has your organisation conducted a formal inventory of non-human identities (service accounts, API keys, OAuth grants, AI agent credentials)?
A) Yes — full NHI inventory with least-privilege enforcement and rotation schedule
B) Partial — major service accounts known, smaller NHIs not fully governed
C) No formal NHI inventory exists
D) We are not aware of the scope of our non-human identity estate.
Q4: Does your organisation have real-time continuous monitoring across all five Zero Trust pillars (identity, device, network, application, data)?
A) Yes — XDR or SIEM with telemetry across all pillars, AI-powered analytics
B) Partial — monitoring covers some pillars but not all
C) Basic — network monitoring only, limited identity and device telemetry
D) Reactive — monitoring is primarily post-incident investigation
Q5: Does your organisation have a defined zero trust policy that answers who, what, when, where, why, and how for all access requests to critical assets?
A) Yes — formally documented, enforced by a segmentation gateway, regularly reviewed
B) Informal — access policies exist but are not formally documented or consistently enforced
C) Legacy — firewall rules and group memberships govern access, not zero trust policy
D) No formal access policy framework exists.
Score Interpretation:
Mostly A: Your organisation demonstrates strong zero trust maturity. Focus on NHI governance, AI workload security, and continuous red team validation.
Mostly B: Partial controls are in place. Prioritise closing the identified gaps — VPN replacement, micro-segmentation, and NHI inventory deliver the highest marginal security return.
Mostly C/D: Significant exposure to lateral movement and credential exploitation exists. Engage a qualified cybersecurity professional to build a sequenced zero-trust implementation roadmap before your next incident.
Related Research and Further Reading
- For the foundational overview covering all major cybersecurity threat vectors in 2026, see the pillar article: [20101P] – Cybersecurity in 2026: The Complete Guide to AI Threats, Zero Trust, and Digital Resilience.
- For the threat context that makes Zero Trust architecture essential — AI-powered attacks operating at machine speed — see the previous cluster article: [20102C] – AI-Powered Cyberattacks 2026: 7 Proven Threats Every Business Must Know.
Final Thoughts
The SecurityWeek 2026 analysis is clear: the internal debate has shifted from whether to implement a Zero Trust architecture to how quickly organisations can eliminate each remaining pocket of implicit trust [5]. The organisations that delay this transition are not maintaining a viable security posture — they are accepting a progressively higher probability of a breach whose blast radius will be limited only by the breadth of the implicit trust relationships that remain in place.
The six-step implementation framework in this guide is sequenced for maximum security return on investment. Begin with protecting your most critical assets, govern every identity, human and non-human, replace VPN with application-specific Zero Trust network access, segment your network, classify and protect your data, and monitor continuously.
None of these steps is technically beyond reach for any organisation. All of them require the commitment to dismantle the comfortable assumption of implicit trust — the assumption that has enabled the majority of significant breaches documented over the past decade. The question for every IT leader in 2026 is not whether Zero Trust architecture is right for their organisation. It is how many more incidents they are willing to sustain before implementing it.
FAQ
Q1: What is Zero Trust architecture in simple terms?
A: Zero Trust architecture is a security model built on the principle of never trust, always verify. Rather than granting broad access to users or devices that are inside the network perimeter, Zero Trust requires every access request — regardless of origin — to be continuously verified against identity, device posture, and application context before access is granted. The model assumes that compromise has already occurred and focuses on limiting the blast radius through micro-segmentation, least-privilege access, and continuous monitoring.
Q2: How long does Zero Trust architecture implementation take?
A: Full Zero Trust implementation typically requires 18–36 months for large enterprises. Smaller organisations deploying cloud-delivered Zero Trust services can achieve foundational controls — phishing-resistant MFA, ZTNA for remote access, and identity governance — within 3–6 months. The most important factor is sequencing: beginning with identity controls and protecting surface definition before attempting network micro-segmentation or data governance, yields faster security returns than attempting to deploy all pillars simultaneously.
Q3: What is the difference between ZTNA and VPN?
A: A VPN establishes an encrypted tunnel that grants broad access to the corporate network after a single authentication event — once inside, users can access all systems their account has permissions to reach.
Zero Trust network access establishes application-specific connections that are individually verified per session, limited to the specific application being accessed, and terminated when the session ends. VPNs create a large lateral movement surface after compromise; ZTNA contains compromise to the specific application being accessed at the moment of breach.
Q4: What does ‘never trust, always verify’ mean in practice?
A: In practice, never trust, always verify means that every access request — regardless of whether it comes from inside or outside the network, from a known device or an unknown one, from a regular employee or a senior executive — is evaluated against a consistent set of criteria before access is granted: is this identity who they claim to be? Is this device in the expected compliance state? Does this user legitimately need access to this specific resource? Has anything unusual occurred in this session? Access is granted only when all criteria are satisfied, and is continuously re-evaluated throughout the session.
Q5: How much does Zero Trust architecture implementation cost?
A: Implementation costs vary significantly by organisation size, existing architecture, and scope of deployment. Evaluating Zero Trust implementation cost and ROI is most effective when measured against breach savings rather than against the absolute deployment budget. Cloud-delivered ZTNA and identity solutions typically operate on per-user subscription models ranging from $10–50 per user per month for enterprise platforms.
The more relevant financial comparison is against breach cost: IBM documents a $2.2 million average reduction in breach costs for organisations with full Zero Trust architecture — a figure that typically exceeds the total implementation cost within two to three years of deployment.
Q6: Can Zero Trust architecture be implemented in stages, or must it be deployed all at once?
A: Zero Trust architecture is explicitly designed for staged implementation — it is a continuous maturity journey, not a single deployment project. The six-step framework in this guide reflects the recommended sequencing: protect surface definition, transaction flow mapping, segmentation gateway deployment, policy creation, continuous monitoring, and NHI governance.
Each stage delivers incremental security improvement while building the foundation for the next. Organisations that attempt full simultaneous deployment across all five pillars typically experience implementation fatigue and fail to sustain the operational discipline that Zero Trust requires.
AI Threats Series Overview
This article is part of the AI Threats Security Series — a technical collection of guides exploring the most dangerous AI-powered attack categories, defensive frameworks, and the steps organizations must take to build resilient security postures in 2026.
References
- [1] CISA. Zero Trust Maturity Model Version 2.0. April 2023: https://www.cisa.gov/sites/default/files/2023-04/zero_trust_maturity_model_v2_508.pdf
- [2] Mordor Intelligence. Zero Trust Security Market Size, Share and Forecast 2026–2031. https://www.mordorintelligence.com/industry-reports/zero-trust-security-market
- [3] Gartner. Zero Trust Network Access Market Guide 2025. Gartner Research. https://www.gartner.com/en/information-technology/topics/zero-trust-security
- [4] Research Nester. Zero Trust Architecture Market Size and Share Report 2035: https://www.researchnester.com/reports/zero-trust-architecture-market/5561
- [5] SecurityWeek. Cyber Insights 2026: Zero Trust and Following the Path. https://www.securityweek.com/cyber-insights-2026-zero-trust-and-following-the-path/
- [6] CIO. Why 81% of Organisations Plan to Adopt Zero Trust by 2026. Zscaler ThreatLabz 2025 VPN Risk Report.
https://www.cio.com/article/3962906/why-81-of-organizations-plan-to-adopt-zero-trust-by-2026.html - [7] NIST. Zero Trust Architecture — Special Publication 800-207. National Institute of Standards and Technology.
https://csrc.nist.gov/publications/detail/sp/800-207/final - [8] IBM. Cost of a Data Breach Report 2025. IBM Security.
https://www.ibm.com/reports/data-breach