Ransomware 3.0 in 2026: How Double Extortion and RaaS Are Targeting Your Business
Your backup strategy will not save you. This is the defining lesson of Ransomware 3.0 in 2026 — and it is the one that most organisations are still learning the expensive way. Ransomware 3.0 in 2026 was present in 44% of all breaches documented by Verizon’s Data Breach Investigations Report, a 37% increase from the prior year. For small and medium-sized businesses, that figure rises to 88%.
⚠ TECHNICAL DISCLAIMER This article is for educational and informational purposes only. It does not constitute professional cybersecurity advice, a security audit, or a product recommendation. Threat statistics reflect published research and may not represent your specific sector or risk profile. Engage qualified cybersecurity professionals before making architectural or policy changes.
The Change Healthcare breach alone — 100 million patient records compromised, $22 million paid in ransom, then re-extorted — illustrates what happens when Ransomware 3.0 2026 operates at full capability: RaaS-delivered attacks, double extortion data theft, AI-accelerated reconnaissance, and a four-day median dwell time that leaves almost no window for detection before the damage is done. This guide explains exactly how Ransomware 3.0 works, which sectors face the highest exposure, and the eight-layered defences that measurably reduce both the probability and the impact of a successful attack.
What Is Ransomware 3.0? How the Threat Evolved in 2026
The first generation of ransomware — crude encryption tools demanding modest Bitcoin payments — bears almost no resemblance to the threat landscape of 2026. Ransomware 3.0 has undergone three distinct evolutionary phases, each adding a layer of coercive capability that makes defence progressively more complex.
Ransomware 1.0 — Encrypt and Demand: Early ransomware encrypted files and demanded payment for a decryption key. Maintaining tested, offline backups was largely sufficient to defeat this model. Recovery was painful but achievable without payment.
Ransomware 2.0 — Double Extortion Emerges: Attackers added data exfiltration to the encryption playbook. Before deploying the encryption payload, they exfiltrate sensitive data to attacker-controlled servers. Victims now face two threats simultaneously: losing access to their systems and having their data published publicly. Backups restore system access but cannot unsteal data. This rendered pure backup strategies inadequate.
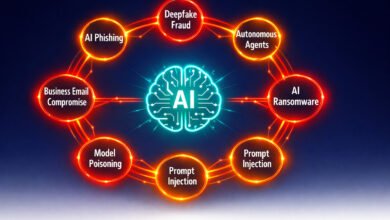
Ransomware 3.0 — AI Acceleration, Triple Extortion, and RaaS at Scale: The current generation combines AI-powered reconnaissance and target selection, double extortion as a baseline tactic, triple extortion extending pressure to regulators, customers, and media, and Ransomware-as-a-Service industrialisation that enables low-skill affiliates to deploy enterprise-grade attack toolkits. Median dwell time has compressed to four days [1], meaning defenders have less than a business week from initial compromise to ransomware deployment.
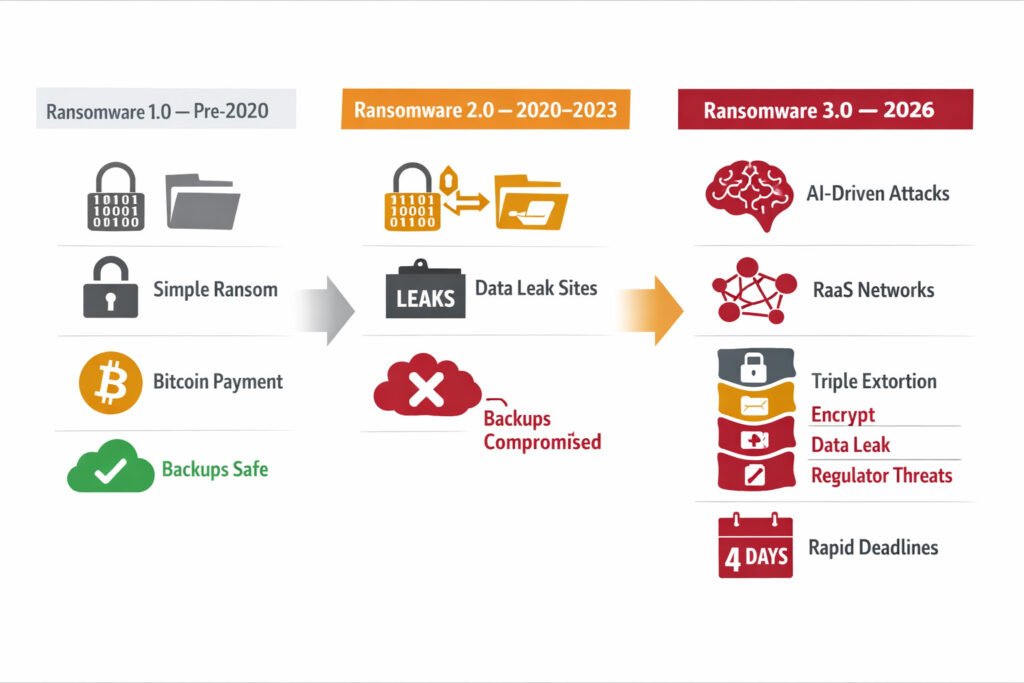
Table 1: Ransomware 3.0 2026 — Key Statistics and Benchmarks
| Metric | Figure | Source | Significance |
| Ransomware in all breaches | 44% of all documented breaches | Verizon DBIR 2025 | 37% increase YoY — majority threat category |
| Ransomware in SMB breaches | 88% of SMB breaches involved ransomware | Verizon DBIR 2025 | SMBs most exposed sector by breach share |
| US ransomware attacks increase | 50% increase in the first 10 months of 2025 [3] | Cyble Research | Accelerating attack volume in the largest market |
| Publicly reported incidents (2025) | 7,200 incidents — 47% increase from 4,900 | Recorded Future | Volume surge despite takedowns |
| Victims refusing to pay | 64% refused payment in 2024 | Chainalysis | Rising — but total damage costs still climbing |
| Median dwell time | 4 days before ransomware deployment | Sophos 2025 | Down from 16 days in 2022 — detection window narrowing |
| Average recovery cost | $4.88 million total incident cost | IBM / TechTimes | Exceeds ransom payment in most cases |
| 85% unreported | Estimated 85% of attacks are not publicly reported | BlackFog [6] | True scale significantly exceeds visible data |
💡 For more information, explore the complete segments of our AI Threats Security Series.
How Ransomware-as-a-Service Works — The Industrialisation of Ransomware 2026
Ransomware 3.0 -as-a-Service has transformed ransomware from a specialist criminal discipline into a commodity marketplace. RaaS developers build and maintain the attack infrastructure — the encryption engine, the negotiation portal, the payment processing system, the leak site — and lease it to affiliate networks on a revenue-sharing model, typically retaining 20–30% of any ransom collected.
The model has achieved a level of operational professionalism that rivals legitimate SaaS businesses. Leading RaaS operations in 2026 offer 24/7 technical support to affiliates, regular product updates incorporating new evasion techniques, negotiation coaching for maximising ransom collection, and dedicated leak sites with individualised victim credentials for affiliate management. The Scattered Spider group — responsible for some of the most damaging 2024–2025 incidents — exemplifies the sophistication of modern RaaS operations: masters of vishing-based MFA bypass, OAuth manipulation, and executive impersonation [2].
The Affiliate Ecosystem
The RaaS affiliate model has separated the technical expertise of ransomware development from the operational expertise of target selection and initial access. Affiliates are recruited for their proficiency in phishing, social engineering, credential theft, and exploit deployment — not for their ability to write malware. This separation has created a horizontal market for initial access brokers: criminal specialists who compromise organisations and sell verified access to RaaS affiliates on dark web marketplaces, allowing affiliates to skip the reconnaissance phase entirely and proceed directly to lateral movement and deployment.
Why Takedowns Have Not Stopped RaaS
Law enforcement takedowns of major RaaS operations — LockBit infrastructure seized in early 2024, REvil and Hive dismantled in prior years — have demonstrated both the capability and the limits of enforcement action. These operations disrupt specific infrastructure and provide decryption keys to existing victims. They do not eliminate the underlying affiliate networks, the tooling expertise, or the criminal financial incentive. Dismantled groups rebrand within weeks — often retaining core affiliates and operational infrastructure under a new identity. 2025 saw 10 significant new RaaS cybersecurity groups emerge to fill the operational void left by enforcement actions [3].
Double Extortion and Triple Extortion — Why Backups Are No Longer Sufficient
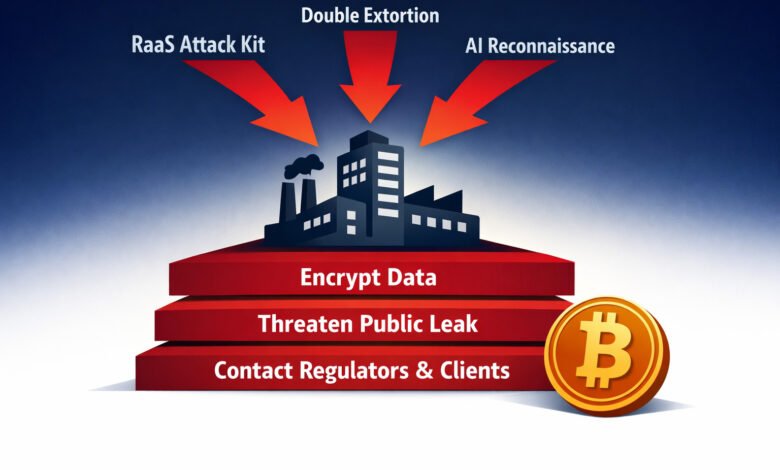
Double extortion ransomware is now the operational standard, not an advanced variant. Cyble’s research confirms that the majority of emerging ransomware groups adopt double extortion immediately because it increases ROI and reduces the victim’s negotiating leverage: even if an organisation can restore from backup, they cannot un-exfiltrate the data already in the attacker’s hands.
The double extortion sequence operates in four stages: first, the attacker gains initial access through phishing, credential theft, or an exposed vulnerability; second, they conduct reconnaissance over days or weeks to identify the highest-value data; third, they exfiltrate that data to attacker-controlled infrastructure; fourth, they deploy the encryption payload and present the victim with two simultaneous demands — pay for the decryption key and pay to prevent publication of the exfiltrated data.
Triple Extortion — Extending Pressure Beyond the Victim
Triple extortion adds a third pressure mechanism: threatening to contact and harm third parties. This may take the form of notifying regulators — as in the documented case where attackers filed an SEC complaint against a victim for failing to disclose a breach within the required four-day window — alerting the victim’s customers directly, approaching the victim’s business partners, or engaging media outlets with the stolen data. The tactical objective is to create pressure from multiple directions simultaneously, reducing the victim’s ability to delay or refuse payment without suffering consequences across multiple stakeholder relationships [4].
Table 2: Ransomware 3.0 Extortion Mechanisms — Comparison and Defensive Response
| Extortion Type | Attack Action | Victim Pressure | Backup Sufficient? | Defensive Priority |
| Single Extortion (1.0) | Encrypt data only | Restore or pay for the key | Yes — tested backups resolve | Immutable offline backups |
| Double Extortion (2.0) | Encrypt + exfiltrate data | Restore OR prevent data leak | No — data already stolen | Data classification + DLP + backups |
| Triple Extortion (3.0) | Encrypt + exfiltrate + contact third parties | Multi-stakeholder pressure simultaneously | No — reputational damage ongoing | Crisis comms plan + legal counsel + DLP |
| Encryption-Free Extortion | Exfiltrate only, no encryption | Quieter — evades backup-based detection | No — no encryption to detect | Data Loss Prevention + UEBA + DLP |
| Quadruple Extortion | Add DDoS to above layers | Operational disruption during negotiation | No — DDoS disrupts recovery | DDoS mitigation + IR retainer + backups |
💡 For more information, explore the complete segments of our AI Threats Security Series.
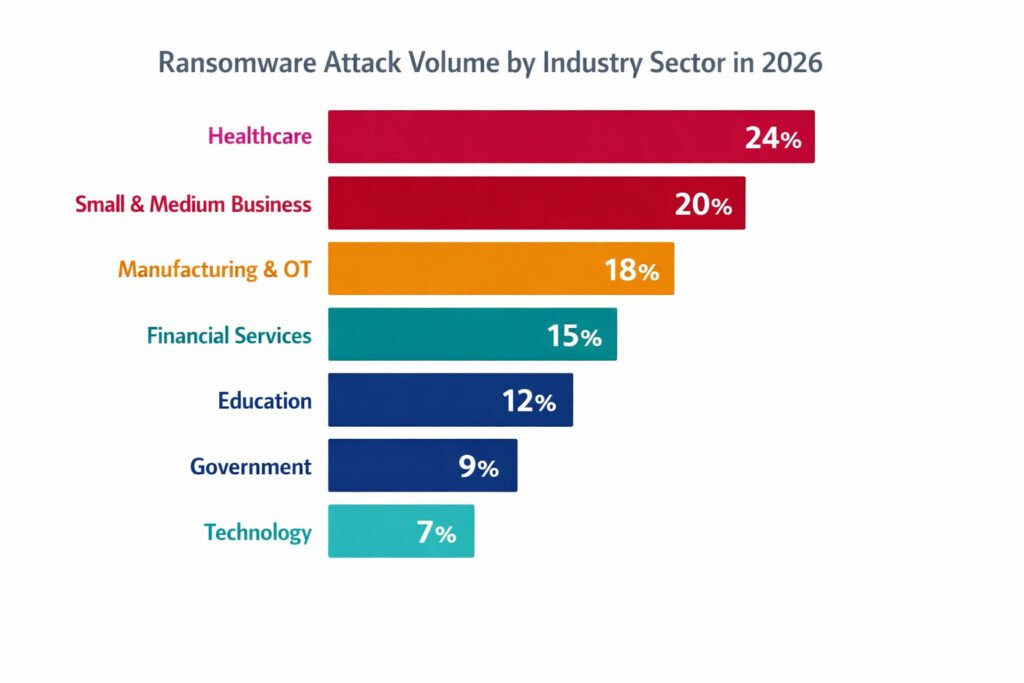
Ransomware 3.0 2026 — Which Industries Face the Highest Exposure
Ransomware does not discriminate — every industry experienced increased attacks in 2024 and 2025. However, certain sectors consistently appear at the top of victim reporting, driven by the combination of high-value data, operational disruption sensitivity, and historically under-resourced security postures.
Healthcare — The Highest-Risk Sector
Healthcare remains the most targeted sector in the Ransomware 3.0 2026 landscape. Patient data commands premium prices on dark web markets, clinical systems cannot be taken offline without direct patient care consequences, and regulatory exposure under HIPAA creates a powerful third-party extortion lever. The Change Healthcare breach — $22 million paid in ransom, nationwide disruption to healthcare billing, and subsequent re-extortion through a second group — established the template for what attackers can achieve against large healthcare organisations. Smaller regional hospitals and clinics face equally severe exposure with a fraction of the security resources.
Small and Medium-Sized Businesses — The Preferred Volume Target
88% of SMB breaches involved ransomware in the Verizon 2025 DBIR. RaaS has made SMB targeting economically efficient: lower defences, faster compromise, and sufficient data value to justify the attack economics even at reduced ransom amounts. Attackers view SMBs as low-hanging fruit — organisations that frequently rely on third-party IT providers, operate with limited dedicated security staff, and maintain inconsistent patch management practices. The ransomware SMB risk in 2026 is not hypothetical — it is the statistical majority of attack volume.
Critical Infrastructure and Manufacturing
Operational Technology (OT) environments — manufacturing floors, industrial control systems, energy infrastructure — represent an expanding ransomware target by 2026. Two-thirds of identified OT ransomware victims are manufacturing firms[8]. Attackers exploit the convergence of IT and OT networks and the catastrophic operational consequences of system unavailability in these environments to maximise payment pressure. The median dwell time compression to four days is particularly dangerous in OT environments where detection capabilities are often less mature than in enterprise IT.
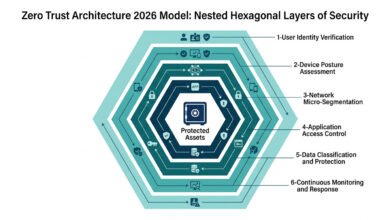
8 Proven Ransomware 3.0 2026 Defences — Building Resilience by Design
The following eight defences represent the evidence-based controls that measurably reduce both the probability of successful Ransomware 3.0 2026 attacks and the impact when an attack succeeds. They are sequenced from foundational to advanced and are applicable at most organisation sizes with appropriate scaling.
Defence 1 — Immutable, Tested, Offline Backups
Backups remain necessary — but they are no longer sufficient alone. The critical word is immutable: backups stored in systems that cannot be modified or deleted by the same credentials that govern production systems. Attackers specifically target backup infrastructure as a first priority — compromising backups before deploying encryption to eliminate the recovery option. Backups must be stored offline or in air-gapped systems, tested for recoverability against defined Recovery Time Objectives (RTOs) at least quarterly, and segmented from the primary network by separate credentials and access controls.
Defence 2 — Data Loss Prevention and Exfiltration Monitoring
Since double extortion ransomware succeeds through data theft before encryption, detecting and blocking abnormal data egress is the most consequential defensive capability that most organisations currently lack. Data Loss Prevention (DLP) tools monitor for large-volume data transfers, unusual access to sensitive data repositories, and exfiltration to non-approved destinations. User and Entity Behaviour Analytics (UEBA) establishes a behavioural baseline for each account and flags deviations — including the reconnaissance and staging activities that precede ransomware deployment.
Defence 3 — Phishing-Resistant MFA Across All Access Points
Identity compromise is now the primary ransomware initial access vector, ahead of vulnerability exploitation. Phishing-resistant multi-factor authentication — hardware security keys or passkeys rather than SMS OTP — eliminates the credential theft vector that RaaS affiliates most frequently exploit. 100% MFA coverage across all internet-facing accounts, privileged accounts, and remote access systems is the single highest-return defensive investment available to any organisation in 2026.
Defence 4 — Endpoint Detection and Response
EDR provides the visibility required to identify the lateral movement, privilege escalation, and reconnaissance activities that characterise the pre-encryption phase of a ransomware attack. Knowing how to detect ransomware before encryption deploys is the defining capability gap in most organisations’ current security posture — and behavioural EDR is the primary tool that closes it.
Understanding how to detect ransomware before encryption deploys is the defining capability gap in most organisations’ current security posture — and behavioural EDR is the primary tool that closes it. Behaviour-based EDR — detecting patterns of activity rather than known malware signatures — is essential against the Living-off-the-Land techniques that modern ransomware operators favour: using legitimate system tools (PowerShell, WMI, Mimikatz) to conduct malicious activities that traditional antivirus does not detect.
Defence 5 — Network Micro-Segmentation
Micro-segmentation limits the blast radius of a ransomware incident by preventing the lateral propagation of encryption across the entire network. A ransomware payload that encrypts one isolated segment cannot automatically traverse to adjacent segments without re-authentication across the segmentation boundary. Combined with strict least-privilege access controls, micro-segmentation transforms a potentially catastrophic organisation-wide encryption event into a contained, recoverable incident.
Defence 6 — Patch Management Velocity
Unpatched vulnerabilities in internet-facing systems — VPNs, RDP services, web applications — remain a primary ransomware initial access vector. Google’s Cybersecurity Forecast 2026 identifies exploitation of zero-days and unpatched known vulnerabilities as a top ransomware priority for RaaS cybersecurity groups in 2026 [5]. Automated patch management that applies critical security updates within 24–72 hours of release, prioritised by external exposure and exploitability, closes the vulnerability windows that automated ransomware scanning tools probe continuously.
Defence 7 — Incident Response Planning and Rehearsal
A ransomware defence 2026 strategy that does not include a rehearsed incident response plan is incomplete. The four-day median dwell time means that organisations may have as little as 72–96 hours from initial access to encryption deployment. An untested incident response plan that has never been executed under pressure is functionally equivalent to no plan. Tabletop exercises simulating ransomware scenarios — including media contact under triple extortion, regulatory notification requirements, and ransom payment decision frameworks — must be conducted at a minimum of annually and ideally quarterly for high-risk sectors.
Defence 8 — Cyber Insurance With Incident Response Retainer
Cyber insurance does not prevent ransomware attacks — but it provides the financial capacity to execute recovery at the required speed and scale, and modern policies increasingly include pre-negotiated incident response retainers with specialist ransomware response firms. The anti-ransomware strategy value of insurance is not the ransom payment itself — 64% of victims now refuse to pay — but the coverage for the $4.88 million average total recovery cost that includes forensic investigation, legal counsel, regulatory notification, business interruption, and remediation services.
Table 3: Ransomware 2026 Defence Framework — Controls Mapped to Attack Phases
| Attack Phase | Attacker Action | Defensive Control | Implementation Priority |
| Initial Access | Phishing, credential theft, VPN exploit | Phishing-resistant MFA + patch management | Critical — deploy first |
| Reconnaissance | Network scanning, data mapping, and privilege escalation | EDR + UEBA + network monitoring | Critical — detect before exfiltration |
| Data Exfiltration | Bulk data transfer to attacker servers | DLP + egress monitoring + UEBA | Critical — double extortion prevention |
| Lateral Movement | Credential abuse, tool deployment across the network | Micro-segmentation + least-privilege access | High — limits blast radius |
| Backup Compromise | Target backup systems before encryption | Immutable offline backups + separate credentials | Critical — recovery dependency |
| Encryption Deployment | Ransomware payload execution | EDR behavioural detection + network segmentation | High — last-resort containment |
| Extortion and Negotiation | Ransom demand, leak threats, regulatory contact | IR plan + legal counsel + crisis comms + insurance | Essential — response capability |
Counter-Arguments: A Critical Discussion on Ransomware Defense Orthodoxy (2026 Model)
Building a resilient defense strategy requires more than just following standard checklists; it demands an honest confrontation with the evolving realities of the threat landscape. In 2026, the traditional orthodoxy of ransomware defence is being challenged by four pivotal debates that redefine our understanding of risk and recovery.
1. The Paradox of Rising Incidents vs. Declining Payments
There is a common misconception that because victims are increasingly refusing to pay—with refusal rates hitting 64%—the ransomware threat is finally receding. However, the data suggests a more complex reality. While payment rates are down, incident volume is surging; Recorded Future noted a 47% increase in reported attacks in 2025, and Cyble reported a 50% spike[3] in US-based attacks during the same period.
What we are witnessing is not a retreat by attackers, but a shift in the battlefield. Larger organizations have successfully matured their backup and recovery capabilities, allowing them to say “no” to extortion. Yet, the financial “sting” remains: total recovery costs still average $4.88 million due to downtime, remediation, and reputational fallout. Attackers are responding to this resilience by increasing attack volume and pivoting to encryption-free, exfiltration-only models that bypass backup-based recovery entirely.
2. The Ransom vs. Recovery Cost Dilemma
A frequent point of contention is whether paying a ransom is a “logical” business decision when the cost of manual recovery far exceeds the demand. This is a high-stakes gamble involving legal, ethical, and operational risks. From a legal standpoint, OFAC sanctions create massive liability for organizations that inadvertently fund designated threat actors.
Practically, payment is never a guarantee of resolution. The Change Healthcare incident serves as a grim case study: even after a $22 million payment, the organization faced re-extortion by a secondary group. Current guidance from the FBI and CISA remains firm: do not pay. The evidence consistently shows that organizations investing in pre-incident resilience achieve faster recovery at a lower total cost than those relying on post-incident negotiations.
3. The SMB capability myth: budget vs. protection
There is a persistent narrative that Small and Medium-Sized Businesses (SMBs) are “sitting ducks” because they cannot afford enterprise-grade defense. This is increasingly untrue in 2026. The five highest-return controls—phishing-resistant MFA, immutable backups, EDR via MSPs, patch automation, and basic DLP—are now accessible through cloud-delivered security platforms at a fraction of the cost of a single breach.
With the rise of Managed Detection and Response (MDR) and security stacks provided by Managed Service Providers (MSPs), the barrier to entry has shifted from technical capability to organizational awareness. The challenge for SMBs today is not the price tag of the tools, but the prioritization of security within their operational culture.
4. The shift to encryption-free ransomware: Is detection obsolete?
The rise of “encryption-free” ransomware—where data is stolen but not locked—has led some to argue that traditional encryption-detection tools are now obsolete. Indeed, these attacks do not trigger the file-system anomalies that older defenses looked for. However, they do not render defense impossible; they simply require a maturation of capabilities.
The defensive response has moved from watching the files to watching the behavior. Tools like Data Loss Prevention (DLP) and User and Entity Behavior Analytics (UEBA) are designed to flag abnormal data egress and the reconnaissance patterns that precede a leak. Rather than making old tools obsolete, this shift reinforces the necessity of a Zero Trust Architecture. It proves that a “backup-only” strategy is no longer a complete defense and strengthens the case for deep investment in behavioral monitoring.
Ransomware defence in 2026 is no longer about stopping the lock — it is about a holistic approach to data sovereignty, behavioural visibility, and the refusal to view payment as a viable recovery pillar.
KNOWLEDGE ASSESSMENT QUIZ: How Resilient Is Your Organisation Against Ransomware 3.0?
⚠ Disclaimer: This quiz is for self-awareness only and does not constitute a security audit or professional recommendation.
Q1: Does your organisation maintain immutable, offline backups that are tested for recoverability at least quarterly?
A) Yes — immutable, air-gapped, tested quarterly with defined RTOs
B) Yes — regular backups, but not tested for recoverability recently
C) Cloud backups only — not offline or tested
D) Backups exist, but the process is informal and untested
Q2: Does your organisation have Data Loss Prevention tools monitoring for abnormal data egress?
A) Yes — DLP deployed across all sensitive data repositories with egress alerting
B) Partial — some monitoring exists, but not comprehensive DLP
C) No formal DLP — we rely on network monitoring only
D) We have not assessed our data exfiltration detection capability
Q3: Has your organisation deployed phishing-resistant MFA (hardware keys or passkeys) across all remote access and privileged accounts?
A) Yes — phishing-resistant MFA on all privileged and internet-facing accounts
B) Yes — SMS-based or app-based MFA (not phishing-resistant)
C) MFA deployed on some accounts only
D) No MFA — password-only authentication
Q4: Does your organisation have a documented, rehearsed ransomware incident response plan?
A) Yes — tabletop exercise conducted within the last 12 months, including ransom decision framework
B) The IR plan exists, but has not been rehearsed
C) Informal procedures only — no documented ransomware IR plan
D) No incident response plan exists
Q5: Is your organisation’s network micro-segmented to limit lateral movement and ransomware propagation?
A) Yes — critical systems isolated with separate access controls
B) Basic VLAN segmentation only
C) Flat network — no meaningful segmentation
D) We have not assessed our network segmentation posture
Score Interpretation:
- Mostly A: Strong ransomware resilience. Focus on DLP maturity, triple extortion response planning, and supply chain risk assessment.
- Mostly B: Foundational controls are partially in place. Prioritise upgrading to phishing-resistant MFA, testing backups, and deploying DLP for exfiltration detection.
- Mostly C/D: Significant exposure across multiple attack phases. Engage a qualified cybersecurity professional immediately to build a sequenced ransomware resilience roadmap before your next incident.
Final Thoughts
Ransomware 3.0 in 2026 is not a threat that any single control can defeat. The organisations that weather ransomware incidents with minimal operational impact share a common architectural posture: phishing-resistant identity controls that eliminate the most prevalent initial access vectors; immutable backups that ensure recovery capability even when production systems are encrypted; data loss prevention that detects exfiltration before the encryption payload deploys; network segmentation that contains propagation; and a rehearsed incident response capability that executes under pressure without improvisation.
The consistent lesson of the Ransomware-as-a-Service era is that resilience is a design outcome, not an emergency response outcome. The organisations that fare worst are those that treat ransomware defence as a technology procurement decision rather than an operational discipline. The four-day dwell time window that separates initial compromise from encryption deployment is not sufficient time to design a response. It is only sufficient time to execute one that has already been designed, tested, and rehearsed. Begin with the eight defences in this guide. Test them. Then test them again.
FAQ
Q1: What is Ransomware-as-a-Service, and why has it increased attack volume so dramatically?
A: Ransomware-as-a-Service is a criminal business model where ransomware developers lease their attack infrastructure — encryption engine, negotiation portal, leak site — to affiliate networks in exchange for 20–30% of ransom proceeds. RaaS has eliminated the technical expertise barrier to launching sophisticated ransomware attacks, enabling low-skill actors to deploy enterprise-grade toolkits.
Recorded Future documented 7,200 publicly reported ransomware incidents in 2025 — a 47% increase — directly attributable to RaaS democratisation. True attack volume is estimated at 6–7 times higher, as approximately 85% of incidents are not publicly reported [6].
Q2: Why are backups no longer sufficient to protect against ransomware in 2026?
A: Double extortion ransomware exfiltrates data before encrypting it. Restoring from backup recovers system access but cannot unsteal data that is already in the attacker’s hands and being threatened for public release.
Triple extortion extends this further: attackers contact regulators, customers, and media with the stolen data, creating pressure independent of system recovery. Backups remain essential for operational recovery — but they must be combined with data loss prevention, egress monitoring, and crisis communications capability to address the full extortion toolkit of Ransomware 3.0.
Q3: Should our organisation pay ransomware if we are attacked?
A: This decision involves legal, ethical, financial, and operational dimensions that require qualified legal and cybersecurity counsel. OFAC sanctions prohibit payment to certain designated threat actors, creating legal exposure. Practically, payment does not guarantee data recovery or prevent re-extortion — the Change Healthcare incident demonstrated both failures.
The FBI and CISA advise against payment while acknowledging that individual organisational circumstances vary. The evidence consistently shows that anti-ransomware investment before an incident costs significantly less than the $4.88 million average total recovery cost after one. Consult your legal counsel and a specialist ransomware response firm before making any payment decision.
Q4: What is the difference between double extortion and triple extortion ransomware?
A: Double extortion combines data encryption with data theft — victims face both system lockout and the threat of data publication. Triple extortion adds a third pressure mechanism: contacting third parties to amplify consequences.
This may include notifying regulators (triggering investigation), contacting the victim’s customers directly (damaging relationships), engaging media with stolen data (reputational damage), or launching DDoS attacks (operational disruption during negotiations). Triple extortion is designed to create pressure from multiple simultaneous directions, reducing the victim’s ability to delay or refuse payment without suffering consequences across multiple stakeholder relationships.
Q5: How quickly can a ransomware attack encrypt an entire organisation’s data?
A: Modern ransomware 2026 can encrypt terabytes of data within minutes of payload deployment. The more relevant timeline is the dwell period before encryption: Sophos reports a median of four days between initial access and encryption deployment.
This four-day window is when attackers conduct reconnaissance, establish persistence, exfiltrate data, and compromise backups. Endpoint Detection and Response tools with behavioural analytics are designed to detect these pre-encryption activities — making early detection during the dwell period the most consequential defensive capability for limiting ransomware impact.
Q6: Are managed service providers (MSPs) safe to use for our cybersecurity, given RaaS supply chain attacks?
A: MSPs represent both a significant ransomware SMB risk vector and the most practical path to enterprise-grade security for most SMBs. RaaS groups specifically target MSPs because compromising one provides access to all managed clients — the Ingram Micro 2025 incident illustrates this one-to-many attack model.
The appropriate response is not to avoid MSPs but to verify their security posture: review their security certifications, confirm their incident response capabilities, ensure contractual clarity on security responsibilities, and verify that your environment is segmented from other MSP clients. A security-mature MSP remains safer than an under-resourced internal IT team.
AI Threats Series Overview
This article is part of the AI Threats Security Series — a technical collection of guides exploring the most dangerous AI-powered attack categories, defensive frameworks, and the steps organizations must take to build resilient security postures in 2026.
References
- [1] Sophos. State of Ransomware Research Hub — 2025 Edition. Sophos.
https://www.sophos.com/en-us/whitepaper/state-of-ransomware - [2] CISA. Scattered Spider Cybersecurity Advisory. November 2023:
https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-320a - [3] Cyble. 10 New Ransomware Groups of 2025 and Threat Trends for 2026. https://cyble.com/knowledge-hub/10-new-ransomware-groups-of-2025-threat-trend-2026/
- [4] SEC. Cybersecurity Disclosure Rules — Enforcement Actions 2024: https://www.sec.gov/newsroom/press-releases/2023/2023-227
- [5] Google Cloud. Cybersecurity Forecast 2026. Google Cloud Security. https://cloud.google.com/security/resources/cybersecurity-forecast
- [6] BlackFog. The State of Ransomware 2025 — Unreported Attack Estimates: https://www.blackfog.com/the-state-of-ransomware-in-2025/
- [7] FBI IC3 — 2025 Annual Report:
https://www.ic3.gov/AnnualReport/Reports/2025_IC3Report.pdf - [8] Dragos. Year in Review: OT Cybersecurity Report 2025:
https://www.dragos.com/year-in-review/