Harvest Now, Decrypt Later (HNDL) Attacks Explained: Why Your Encrypted Data Is Already at Risk in 2026
Your organization’s most sensitive encrypted data may already be in an adversary’s archive. Not because encryption failed, but because of the Harvest Now, Decrypt Later (HNDL) threat model.
In an HNDL attack, adversaries collect encrypted data today and store it for future decryption using quantum computers. This means data that appears secure in 2026 may become fully readable in the next decade.
Security agencies already treat HNDL as an active threat—not a theoretical one.
Understanding the Harvest Now, Decrypt Later (HNDL) threat is no longer optional for security leaders. The NSA, CISA, and NIST issued a joint advisory explicitly warning that adversaries may already be harvesting encrypted data with long-term strategic value — with the intent to decrypt it once large-scale quantum computers emerge. This guide explains what a harvest-now, decrypt-later attack is, how it operates in practice, which organizations face the highest exposure, and what concrete steps reduce that exposure starting today.
⚠ Technical Disclaimer: This article is for educational and informational purposes only. It does not constitute professional cybersecurity, cryptographic, or legal advice. Cryptographic migration involves complex technical, regulatory, and operational dimensions. Organizations should engage qualified professionals before implementing cryptographic changes.
What Is a Harvest Now, Decrypt Later Attack — The Core Threat Model
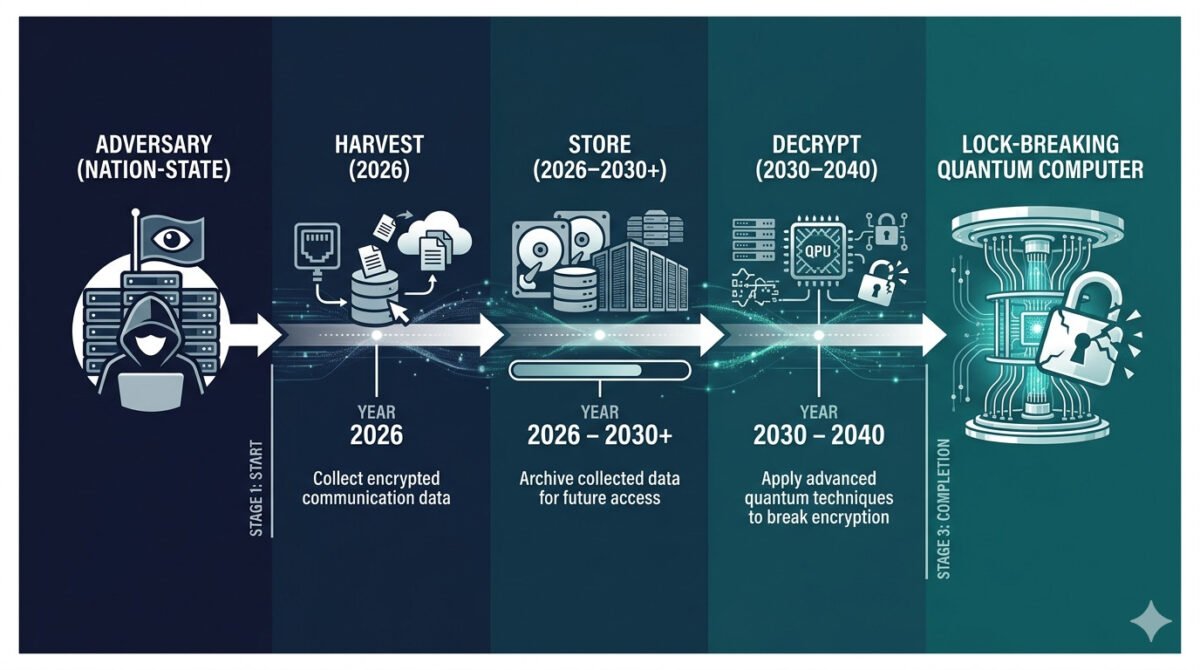
A Harvest Now, Decrypt Later attack is a two-stage strategy:
- Collection phase – Encrypted data is intercepted and stored
- Decryption phase – Data is decrypted later using quantum computing
The HNDL model removes the need to break encryption in real time. Instead, attackers rely on future capabilities.
This creates a critical asymmetry:
- Attackers rely on future decryption power
- Defenders rely on the current encryption strength
The attack exploits a fundamental asymmetry: the adversary does not need to break encryption today. Modern public-key encryption algorithms — RSA, Elliptic Curve Cryptography (ECC), and Diffie-Hellman key exchange — rely on mathematical problems that classical computers cannot solve in practical time. Shor’s algorithm, executable on a sufficiently powerful quantum computer, can solve both the integer factorization problem underlying RSA and the discrete logarithm problem underlying ECC efficiently. Once a CRQC exists, all data ever encrypted with these algorithms becomes retroactively readable.
Why HNDL Is a Serious Threat in 2026
The key risk behind HNDL attacks is time.
If encrypted data is harvested today and decrypted in 2032, the breach effectively already happened in 2026.
Organizations often misunderstand this timeline. Post-quantum migration completed later will not protect already captured data. This is why HNDL is considered a present-day risk.
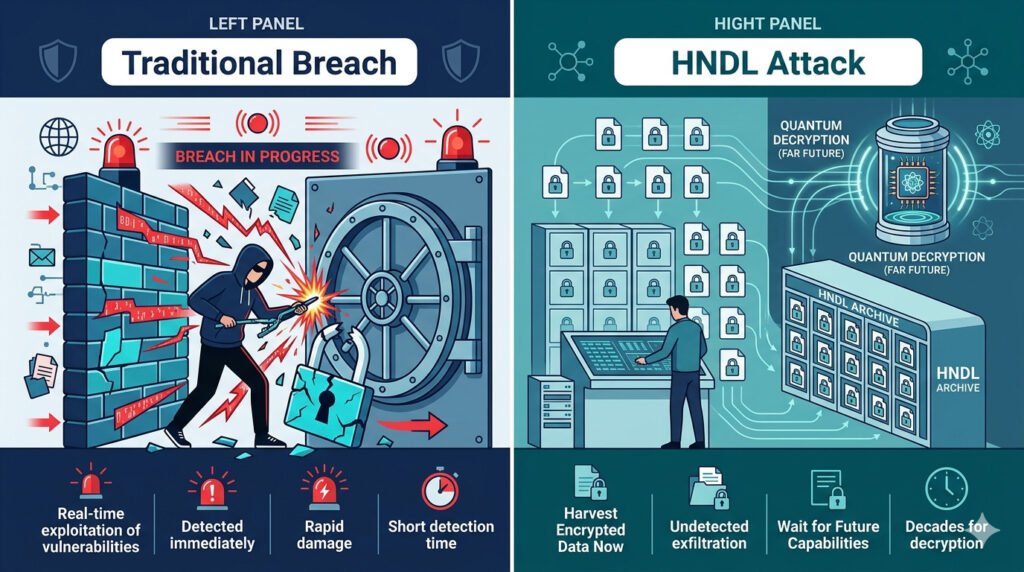
Key distinction: A traditional breach gives you a recovery window. An HNDL attack gives you none — retroactive protection after collection has occurred is technically impossible. The only defense is prospective: deploy quantum-safe encryption before collection occurs.
How HNDL Attacks Work (3 Stages)
1. Data Collection
Attackers collect encrypted data through:
- Network interception
- Compromised infrastructure
- Cloud data exfiltration
Because the data remains encrypted, detection is extremely difficult.
2. Long-Term Storage
The collected ciphertext is stored for years.
Modern storage costs are low enough to make large-scale HNDL operations feasible, especially for nation-state actors.
3. Future Decryption
Once quantum computers reach sufficient scale, attackers apply quantum algorithms to break encryption.
At that point, all previously harvested data becomes readable.
HNDL Attacks vs. Traditional Breaches — Key Differences
Table 1: How the Harvest Now, Decrypt Later threat model differs from conventional cyberattacks across six dimensions that shape both risk assessment and defensive strategy.
| Attribute | Traditional Cyber Breach | HNDL Attack | Security Implication |
| Detection window | Hours to weeks — anomalous activity visible | Zero — no active intrusion signature | HNDL breaches may already be undetected |
| Attack timing | Exploit and exfiltrate immediately | Collect now — decrypt years later | Damage occurs after quantum capability arrives |
| Data usability | Attacker reads data at breach time | Data is encrypted and unreadable today | Breach value is deferred — not absent |
| Encryption protection | Encryption prevents reading stolen data | Encryption is the future target, not the shield | RSA/ECC provides no long-term HNDL protection |
| Primary threat actor | Criminal groups, ransomware operators | Nation-states with strategic patience | Requires state-level storage and coordination |
| Countermeasure timeline | Incident response after breach | Must migrate before CRQC arrives | Reactive defense is permanently too late |
The HNDL threat model fundamentally changes how risk must be managed.
Which Organizations Face the Highest Harvest Now, Decrypt Later Risk
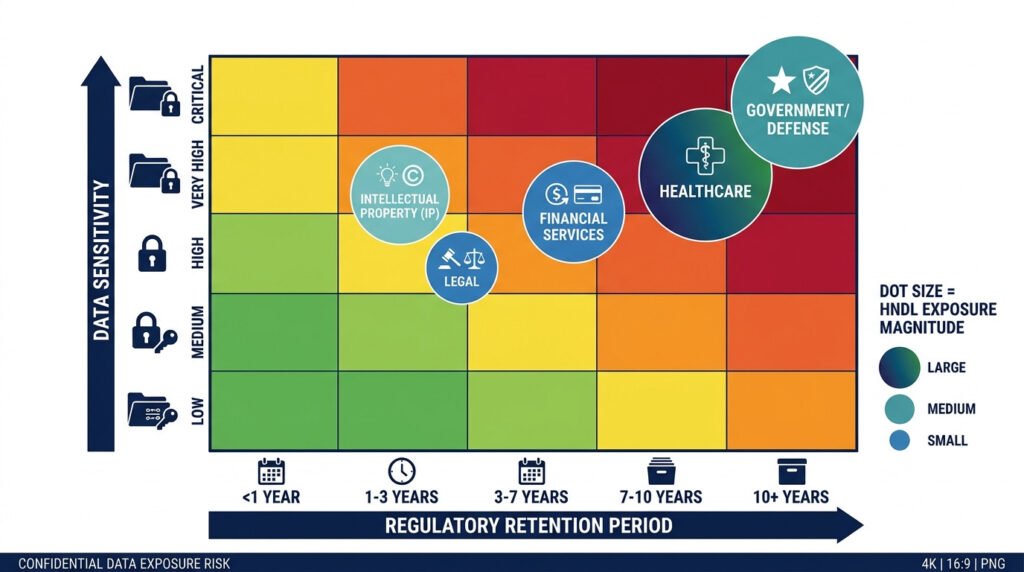
HNDL attack exposure is not uniform across organizations. The critical variable is data confidentiality lifetime — how long a given piece of information must remain secret. An adversary storing traffic captured in 2026 derives maximum value from data that will still be sensitive when a CRQC arrives in 2032 or beyond. Organizations whose data remains sensitive for five or more years beyond the estimated CRQC arrival window carry the highest Harvest Now, Decrypt Later(HNDL) exposure today.
The Federal Reserve published a 2025 analysis of Harvest Now, Decrypt Later (HNDL) risk applied to distributed financial ledger networks, noting that transaction records captured today could be retroactively decrypted, exposing previously protected financial data at scale. Healthcare organizations face a structurally similar problem: HIPAA mandates six years of record retention, and genomic data is sensitive for a patient’s lifetime. Any encryption protecting that data today will need to survive until at least 2035 — a window that falls squarely within HNDL threat projections.
Table 2: Sectors with the highest Harvest Now, Decrypt Later exposure and the data categories that drive that risk.
| Sector | High-Risk Data Categories | Why HNDL Exposure Is High |
|---|---|---|
| Government and defense | Diplomatic cables, intelligence archives, classified communications | Data sensitivity persists for decades; nation-states are primary adversaries with strategic patience |
| Healthcare | Patient records, genomic data, clinical research | HIPAA mandates 6-year retention, and genomic data is permanently sensitive — both fall squarely within the CRQC arrival window, making the quantum threat to healthcare data acute. Breach impact is visible only after future decryption. |
| Financial services | Transaction histories, trading algorithms, M&A documents, regulatory filings | Financial data enables fraud and market manipulation years after collection; regulatory retention windows extend exposure |
| Intellectual property | Product designs, R&D data, patents, aerospace, and defense contracts | Proprietary advantage survives for product lifecycles measured in decades; IP theft compounds over time |
| Legal and law firms | Client communications, litigation strategy, privileged documents | Attorney-client privilege applies indefinitely; adversaries strive to gain long-term strategic leverage |
Why HNDL Is Treated as an Active Threat in 2026 — Not a Future Scenario
For those assessing the quantum threat to encrypted data in 2026, the evidence base — while classified — is sufficient for the NSA, CISA, and NIST to issue joint public warnings, and for Google to accelerate its migration timeline specifically in response [1][8].
The most important framing shift required to understand Harvest Now, Decrypt Later (HNDL) correctly is temporal. Most organizations instinctively categorize quantum threats as a future problem — something to address when quantum computers actually arrive. This framing is incorrect for any organization whose data must remain confidential past 2030.
If a nation-state adversary collects your encrypted data today and decrypts it in 2033, the breach occurred in 2026. No post-quantum migration completed in 2028 will protect data that was already collected. The only window in which HNDL collection can be prevented is before it occurs.
This is why the NSA, CISA, and NIST jointly issued guidance in 2023 warning that organizations should assume adversaries are actively harvesting encrypted data with long-term strategic value. Google accelerated post-quantum cryptography deployment across its platforms — including Android — citing quantum-era security as an immediate priority rather than a future concern [8]. The U.S. National Security Memorandum 10 established a 2035 federal migration deadline specifically because of HNDL exposure to currently encrypted national security data.
Cloudflare, which processes a substantial share of global internet traffic, deployed hybrid post-quantum key exchange — combining ML-KEM with the classical X25519 algorithm — at internet scale, explicitly citing HNDL attack risk reduction as a driver. By late 2025, over 50 percent of web traffic traversing Cloudflare’s network was protected by hybrid post-quantum key exchange [3]. This is not theoretical preparedness. It is an operational deployment by one of the largest internet infrastructure providers in the world, treating HNDL as a present-tense risk.
Regulatory signal: NSA CNSA 2.0 mandates quantum-resistant algorithms for all new National Security System acquisitions by January 1, 2027. Organizations in the defense supply chain cannot treat HNDL as a future-planning concern — it is an imminent compliance requirement.
💡 For more information, explore the complete segments of our PQC Series
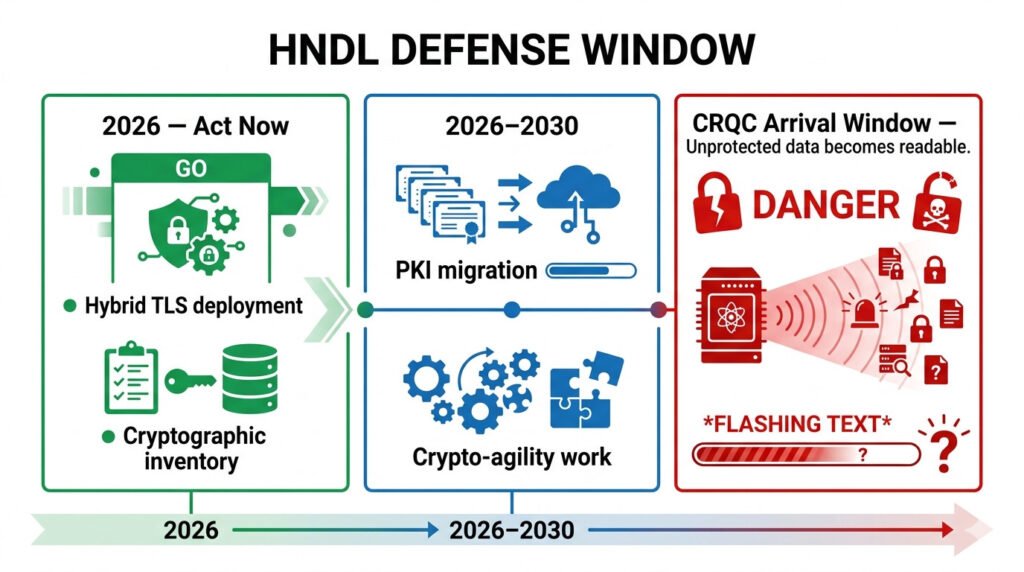
Defending Against Harvest Now, Decrypt Later Attacks — What Organizations Must Do Now
HNDL defense operates on a single constraint: all protective action must occur before a CRQC exists. Post-migration protection applies only to data encrypted after the migration is complete. This means the priority is reducing the volume of long-lived sensitive data still protected by quantum-vulnerable encryption — starting with data that faces the highest confidentiality-lifetime risk.
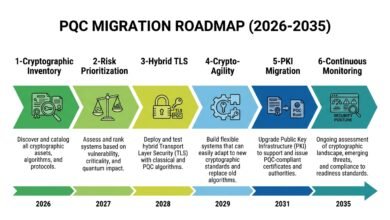
For the complete six-phase enterprise migration roadmap aligned with NIST standards, see the related guide: Post-Quantum Cryptography 2026: Why Your Encryption Strategy Must Change Now.
The immediate first step for every organization is a cryptographic inventory — mapping every system, protocol, certificate, and key that uses RSA, ECC, or Diffie-Hellman. Without this inventory, it is impossible to prioritize migration or measure HNDL exposure. NIST SP 1800-38C guides cryptographic discovery tools that can automate inventory creation across enterprise environments.
For internet-facing communications, the most impactful near-term action is deploying hybrid TLS using ML-KEM + X25519 key exchange. This combination — already deployed by Cloudflare and Google at internet scale — provides immediate HNDL attack protection for new traffic while maintaining compatibility with classical systems that have not yet completed their own migrations. New traffic encrypted with ML-KEM hybrid is resistant to future quantum decryption even if a CRQC arrives before full PKI migration is complete.
Table 3: HNDL mitigation strategies compared by risk reduction, implementation complexity, and recommended deployment timeline for 2026.
| Mitigation | HNDL Risk Reduction | Implementation Complexity | Recommended Start |
| Hybrid TLS (ML-KEM + X25519) | High — protects new traffic immediately | Low — Cloudflare/Google deployed at scale | Immediately — 2026 |
| Cryptographic inventory (CBOM) | Medium — identifies exposure scope | Medium — requires tooling and process | Immediately — prerequisite for all steps |
| PKI migration to ML-DSA | High — eliminates signature vulnerability | High — PKI ecosystem coordination required | 2026–2028 |
| Data minimization and deletion | Medium — reduces the harvesting target surface | Low — policy and process change | Immediately — reduces legacy exposure |
| Forward-secure protocol adoption | High — limits retrospective decryption | Medium — protocol configuration changes | Short-term — 2026 |
| Full PQC migration (no hybrid) | Maximum — eliminates all quantum exposure | Very High — full system re-engineering | Target complete by 2030–2035 |
Counter-Arguments: Four Honest Challenges to HNDL Urgency
Objection: No confirmed evidence of Harvest Now, Decrypt Later operations exists in the public domain — organizations should not respond to speculative threats.
Discussion: This objection conflates public disclosure with operational reality. Intelligence collection operations are, by design, not publicly disclosed. The NSA, CISA, and NIST issued joint guidance in 2023 explicitly warning that adversaries may already be harvesting data — language calibrated to acknowledged classified intelligence rather than speculation.
Google cited Harvest Now, Decrypt Later (HNDL) attack as a primary motivator for its 2026 migration announcement. The absence of public confirmation is a feature of covert intelligence operations, not evidence of their absence.
Solution: Organizations should adopt the same risk posture as their security agencies: assume collection is occurring for any data whose confidentiality lifetime extends beyond 2030, and migrate accordingly.
Objection: Quantum computers are decades away — Harvest Now, Decrypt Later(HNDL) urgency is being overstated to drive unnecessary security spending.
Discussion: The quantum timeline debate misunderstands the HNDL threat structure. The question is not when a CRQC will exist, but whether your data must remain confidential until after it exists.
Healthcare records retained under HIPAA, classified government communications, and genomic data all carry confidentiality requirements that extend well into the 2030s and beyond. For this data, HNDL exposure is a present-tense operational risk regardless of where quantum timelines ultimately land. Google’s internal timeline targets 2029 for PQC migration completion — a schedule driven by this exact logic.
Solution: Apply Mosca’s Theorem to your specific data categories. If your data retention period plus your post-quantum migration timeline exceeds the estimated CRQC arrival window — currently projected at 2030–2040 — migration is already overdue for that data class. Organizations that have not begun mapping their post-quantum migration timeline against CRQC projections are accumulating HNDL exposure with each passing month.

Objection: Symmetric encryption such as AES-256 is quantum-resistant — organizations using it are already protected against HNDL attack.
Discussion: Symmetric encryption does provide better quantum resistance than RSA or ECC: Grover’s algorithm reduces AES-256 effective security to AES-128 levels — still computationally infeasible to break. However, symmetric encryption is not used to protect data in transit in isolation.
TLS handshakes, VPN connections, and key exchange protocols rely on asymmetric public-key cryptography — RSA or ECDH — to establish the session keys that protect symmetric encryption.
An adversary who archives the TLS handshake alongside the encrypted traffic can later use Shor’s algorithm to recover the session key and decrypt the symmetric ciphertext. The full protocol stack must be migrated, not only the symmetric layer.
Solution: Audit the full cryptographic protocol stack, not only the symmetric encryption layer. Hybrid TLS deployment ensures the key exchange mechanism — not only the bulk encryption — is quantum-resistant.
Objection: Post-quantum cryptography algorithms are unproven and may introduce new vulnerabilities — migrating now is premature.
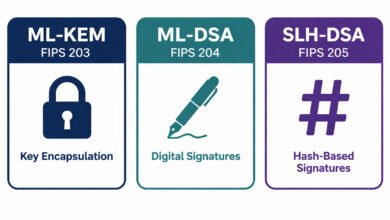
Discussion: The NIST PQC standards — ML-KEM (FIPS 203), ML-DSA (FIPS 204), and SLH-DSA (FIPS 205) — completed an eight-year international evaluation process involving hundreds of cryptographers across more than 25 countries.
No practical vulnerabilities have been identified as of 2026. The concern about unproven algorithms is addressed directly by the NIST-recommended hybrid approach: deploying ML-KEM alongside X25519 means an attacker must break both the classical and post-quantum components to compromise the session. Hybrid deployment eliminates the binary risk of either approach used alone.
Solution: Deploy hybrid cryptography rather than choosing between classical and post-quantum algorithms. This approach is explicitly endorsed by NIST, reduces risk during the transition period, and is already proven at internet scale by Cloudflare and Google.
Knowledge Assessment Quiz: How Well Do You Understand HNDL Risk?
⚠ Disclaimer: This quiz is for self-awareness only and does not constitute a professional assessment.
Q1: What is the defining characteristic that separates a Harvest Now, Decrypt Later attack from a traditional data breach?
- A) The attacker uses zero-day vulnerabilities to bypass all defenses
- B) The attacker collects encrypted data today and defers decryption until a quantum computer is available
- C) The attacker decrypts data in real time using classical computing clusters
- D) The attacker targets only unencrypted data stored in cloud repositories
Q2: Which of the following data types carries the highest Harvest Now, Decrypt Later exposure for most organizations?
- A) Short-lived session tokens and temporary authentication cookies
- B) Cached web assets and public marketing materials
- C) Healthcare records, genomic data, and classified communications with multi-decade sensitivity
- D) Publicly available press releases and financial disclosures
Q3: Which immediate action provides the most effective near-term reduction of HNDL risk for internet-facing systems?
- A) Disabling all encrypted communications until a quantum-safe protocol is available
- B) Deploying hybrid TLS using ML-KEM + X25519 key exchange
- C) Migrating all databases to AES-128 symmetric encryption
- D) Waiting for NIST to finalize additional post-quantum standards before acting
Score Interpretation:
All correct (Q1: B, Q2: C, Q3: B): Strong HNDL awareness.
Mostly correct: Review the questions you missed — focus on the confidentiality-lifetime concept.
One or more incorrect: Return to the HNDL mechanics section and the sectors table above
FAQ
Q1: Is there confirmed proof that HNDL attacks are happening right now?
A: No Western government has released a public, unclassified confirmation of a named HNDL attack operation as of 2026. However, the NSA, CISA, and NIST jointly stated in 2023 that adversaries may already be harvesting encrypted data — language derived from classified threat assessments.
Google cited HNDL as a primary motivator for its 2029 migration target announced in March 2026. The standard security posture is to assume HNDL collection is occurring for any sensitive data whose confidentiality lifetime extends past 2030.
Q2: What data is most at risk from a harvest now decrypt later attack?
A: Data with confidentiality requirements extending beyond the projected CRQC arrival window — roughly 2030 to 2040 — carries the highest HNDL exposure. This includes healthcare records, classified government communications, genomic data, financial transaction histories, intellectual property with long commercial lifecycles, and legal privileged communications.
Short-lived session data — authentication tokens, temporary credentials — carries minimal HNDL exposure because it loses value long before a CRQC arrives.
Q3: Does encrypting data with AES-256 protect against HNDL?
A: AES-256 provides quantum-resistant bulk encryption — Grover’s algorithm reduces it to AES-128 security levels, which remains computationally infeasible to break. However, TLS and VPN protocols use RSA or ECDH key exchange to establish the session keys that protect AES encryption.
A Harvest Now, Decrypt Later adversary who captures the full TLS session — including the handshake — can later use Shor’s algorithm to recover the session key and decrypt the AES-protected content. The full protocol stack requires migration, not only the symmetric layer.
Q4: Does completing post-quantum migration after 2026 protect already-harvested data?
A: No — this is the most critical aspect of the HNDL threat model. Migration completed after data has been collected provides zero retroactive protection. Any data encrypted with quantum-vulnerable algorithms and captured before migration is complete remains permanently exposed to future quantum decryption. This is why the priority is reducing new HNDL exposure immediately — through hybrid TLS deployment — rather than waiting for full migration to be complete.
Q5: How is HNDL different from a standard data breach?
A: A standard breach requires the attacker to exploit a system at the time of the attack, and encryption of the stolen data limits its immediate usability. HNDL separates collection from exploitation by years or decades — the attacker collects encrypted data that is unreadable today and waits for quantum computing to make it readable.
Standard breach response — incident response, notification, remediation — does not affect HNDL-collected data because the collection leaves no immediate alert. The only defense is prospective encryption migration before collection occurs.
Q6: What is the fastest way to reduce HNDL exposure in 2026?
A: Deploying hybrid TLS using ML-KEM + X25519 on internet-facing services provides the fastest and most impactful near-term protection. New traffic protected by this hybrid configuration is resistant to future quantum decryption even if a CRQC arrives before full PKI migration is complete.
Cloudflare and Google have validated this approach at internet scale. The second immediate action is completing a cryptographic inventory to identify which systems and data carry the highest confidentiality-lifetime risk.
Q7: Does the 2035 NIST deprecation deadline mean organizations have until 2035 to address HNDL?
A: No. The 2035 deadline governs when quantum-vulnerable algorithms must be deprecated.
It does not retroactively protect data encrypted before that deadline. An organization that completes its migration in 2035 will have spent the preceding nine years generating data encrypted with RSA and ECC — all of which remains vulnerable to HNDL decryption once a CRQC exists. The HNDL migration priority should be defined by data confidentiality lifetime, not by the deprecation calendar.
PQC Series Overview
This article is part of the Post-Quantum Security Series — a technical collection of guides exploring cryptographic vulnerabilities exposed by quantum computing, migration strategies for organizations, and the steps required to protect sensitive data before quantum decryption becomes operationally viable.
References
- [1] NSA, CISA, and NIST. Post-Quantum Cryptography: Quantum Readiness — Migrate to Post-Quantum Cryptography. August 2023.https://www.nsa.gov/Press-Room/Press-Releases-Statements/Press-Release-View/article/3498776/
- [2] NIST. FIPS 203, 204, 205 — Post-Quantum Cryptography Standards. August 2024. https://csrc.nist.gov/news/2024/postquantum-cryptography-fips-approved
- [3] Cloudflare Research. NIST’s First Post-Quantum Standards — What This Means for the Internet. https://blog.cloudflare.com/nists-first-post-quantum-standards/
- [4] Federal Reserve Board. Harvest Now, Decrypt Later: Examining Post-Quantum Cryptography and the Data Privacy Risks for Distributed Ledger Networks. 2025. https://www.federalreserve.gov/econres/feds/harvest-now-decrypt-later-examining-post-quantum-cryptography-and-the-data-privacy-risks-for-distributed-ledger-networks.htm
- [5] ENISA: Post-Quantum Cryptography — Current State and Quantum Mitigation. 2021: https://www.enisa.europa.eu/publications/post-quantum-cryptography-current-state-and-quantum-mitigation
- [6] Mosca, M. and Piani, M. Quantum Threat Timeline Report 2024. Global Risk Institute. December 2024. https://globalriskinstitute.org/publication/2024-quantum-threat-timeline-report/
- [7] NIST. IR 8547 — Transition to Post-Quantum Cryptography Standards. 2024. https://nvlpubs.nist.gov/nistpubs/ir/2024/NIST.IR.8547.ipd.pdf
- [8] NSA. Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) FAQ. December 2024 Ver. 2.1. https://media.defense.gov/2024/Dec/06/2003358529/-1/-1/0/CSI_CNSA_2.0_FAQ_V2.1.PDF